CEH v11
INDEX
- Set 1 (Q1 to Q30)
- Set 2 (Q31 to Q60)
- Set 3 (Q61 to Q90)
- Set 4 (Q91 to Q120)
- Set 5 (Q121 to Q150)
- Set 6 (Q151 to Q180)
- Set 7 (Q181 to Q210)
- Set 8 (Q211 to Q240)
- Set 9 (Q241 to Q270)
- Set 10 (Q271 to Q300)
- Set 11 (Q301 to Q330)
- Set 12 (Q331 to Q360)
- Set 13 (Q361 to Q390)
- Set 14 (Q391 to Q420)
- Set 15 (Q421 to Q450)
- Set 16 (Q451 to Q480)
- Set 17 (Q481 to Q510)
- Set 18 (Q511 to Q540)
- Set 19 (Q541 to Q570)
- Set 20 (Q571 to Q600)
- Set 21 (Q601 to Q630)
- Set 22 (Q631 to Q660)
- Set 23 (Q661 to Q690)
- Set 24 (Q691 to Q720)
Q151 - Which Intrusion Detection System is best applicable for large environments where criticalassets on the network need extra security and is ideal for observing sensitive network segments?
- Network-based intrusion detection system (NIDS)
- Host-based intrusion detection system (HIDS)
- Firewalls
- Honeypots
Answer: A
Q152 - Which tool can be used to silently copy files from USB devices?
- USB Grabber
- USB Dumper
- USB Sniffer
- USB Snoopy
Answer: B
Q153 - The following is part of a log file taken from the machine on the network with the IP address of 192.168.1.106: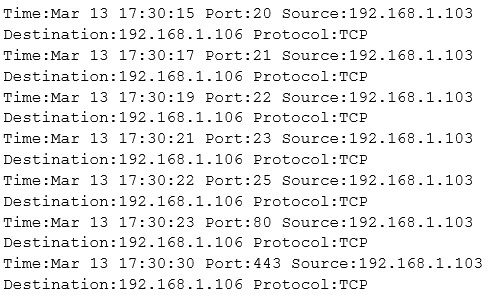
What type of activity has been logged?
- Port scan targeting 192.168.1.103
- Teardrop attack targeting 192.168.1.106
- Denial of service attack targeting 192.168.1.103
- Port scan targeting 192.168.1.106
Answer: D
Q154 - How does a denial-of-service attack work?
- A hacker prevents a legitimate user (or group of users) from accessing a service
- A hacker uses every character, word, or letter he or she can think of to defeat authentication
- A hacker tries to decipher a password by using a system, which subsequently crashes the network
- A hacker attempts to imitate a legitimate user by confusing a computer or even another person
Answer: A
Q155 - Which type of security document is written with specific step-by-step details?
- Process
- Procedure
- Policy
- Paradigm
Answer: B
Q156 - On performing a risk assessment, you need to determine the potential impacts when some of the critical business process of the company interrupt its service. What is the name of the process by which you can determine those critical business?
- Risk Mitigation
- Emergency Plan Response (EPR)
- Disaster Recovery Planning (DRP)
- Business Impact Analysis (BIA)
Answer: D
Q157 - Why would an attacker want to perform a scan on port 137?
- To discover proxy servers on a network
- To disrupt the NetBIOS SMB service on the target host
- To check for file and print sharing on Windows systems
- To discover information about a target host using NBTSTAT
Answer: D
Q158 - Which of the following is an example of two factor authentication?
- PIN Number and Birth Date
- Username and Password
- Digital Certificate and Hardware Token
- Fingerprint and Smartcard ID
Answer: D
Q159 - Which of the following is the BEST way to defend against network sniffing?
- Using encryption protocols to secure network communications
- Register all machines MAC Address in a Centralized Database
- Restrict Physical Access to Server Rooms hosting Critical Servers
- Use Static IP Address
Answer: A
Q160 - Bob finished a C programming course and created a small C application to monitor the network traffic and produce alerts when any origin sends "many" IP packets, based on the average number of packets sent by all origins and using some thresholds. In concept, the solution developed by Bob is actually:
- Just a network monitoring tool
- A signature-based IDS
- A hybrid IDS
- A behavior-based IDS
Answer: A
Q161 - An NMAP scan of a server shows port 25 is open. What risk could this pose?
- Open printer sharing
- Web portal data leak
- Clear text authentication
- Active mail relay
Answer: D
Q162 - Which of the following problems can be solved by using Wireshark?
- Tracking version changes of source code
- Checking creation dates on all webpages on a server
- Resetting the administrator password on multiple systems
- Troubleshooting communication resets between two systems
Answer: D
Q163 - What kind of risk will remain even if all theoretically possible safety measures would be applied?
- Residual risk
- Inherent risk
- Impact risk
- Deferred risk
Answer: A
Q164 - Peter extracts the SIDs list from Windows 2000 Server machine using the hacking tool "SIDExtractor". Here is the output of the SIDs:
From the above list identify the user account with System Administrator privileges.
- John
- Rebecca
- Sheela
- Shawn
- Somia
- Chang
- Micah
Answer: F
Q165 - When a normal TCP connection starts, a destination host receives a SYN (synchronize/start) packet from a source host and sends back a SYN/ACK (synchronize acknowledge). The destination host must then hear an ACK (acknowledge) of the SYN/ACK before the connection is established. This is referred to as the "TCP three-way handshake." While waiting for the ACK to the SYN ACK, a connection queue of finite size on the destination host keeps track of connections waiting to be completed. This queue typically empties quickly since the ACK is expected to arrive a few milliseconds after the SYN ACK. How would an attacker exploit this design by launching TCP SYN attack?
- Attacker generates TCP SYN packets with random destination addresses towards a victim host
- Attacker floods TCP SYN packets with random source addresses towards a victim host
- Attacker generates TCP ACK packets with random source addresses towards a victim host
- Attacker generates TCP RST packets with random source addresses towards a victim host
Answer: B
Q166 - An NMAP scan of a server shows port 69 is open. What risk could this pose?
- Unauthenticated access
- Weak SSL version
- Cleartext login
- Web portal data leak
Answer: A
Q167 - Which of the following is the least-likely physical characteristic to be used in biometric control that supports a large company?
- Height and Weight
- Voice
- Fingerprints
- Iris patterns
Answer: A
Q168 - Which component of IPsec performs protocol-level functions that are required to encrypt and decrypt the packets?
- Internet Key Exchange (IKE)
- Oakley
- IPsec Policy Agent
- IPsec driver
Answer: A
Q169 - Your company was hired by a small healthcare provider to perform a technical assessment on the network. What is the best approach for discovering vulnerabilities on a Windows-based computer?
- Use a scan tool like Nessus
- Use the built-in Windows Update tool
- Check MITRE.org for the latest list of CVE findings
- Create a disk image of a clean Windows installation
Answer: A
Q170 - Which mode of IPSec should you use to assure security and confidentiality of data within the same LAN?
- ESP transport mode
- AH permiscuous
- ESP confidential
- AH Tunnel mode
Answer: A
Q171 - Which of the following tools performs comprehensive tests against web servers, including dangerous files and CGIs?
- Nikto
- Snort
- John the Ripper
- Dsniff
Answer: A
Q172 - In the context of password security, a simple dictionary attack involves loading a dictionary file (a text file full of dictionary words) into a cracking application such as L0phtCrack or John the Ripper, and running it against user accounts located by the application. The larger the word and word fragment selection, the more effective the dictionary attack is. The brute force method is the most inclusive, although slow. It usually tries every possible letter and number combination in its automated exploration. If you would use both brute force and dictionary methods combined together to have variation of words, what would you call such an attack?
- Full Blown
- Thorough
- Hybrid
- BruteDics
Answer: C
Q173 - A company is using Windows Server 2003 for its Active Directory (AD). What is the most efficient way to crack the passwords for the AD users?
- Perform a dictionary attack.
- Perform a brute force attack.
- Perform an attack with a rainbow table.
- Perform a hybrid attack.
Answer: C
Q174 - Initiating an attack against targeted businesses and organizations, threat actors compromise a carefully selected website by inserting an exploit resulting in malware infection. The attackers run exploits on well-known and trusted sites likely to be visited by their targeted victims. Aside from carefully choosing sites to compromise, these attacks are known to incorporate zero-day exploits that target unpatched vulnerabilities. Thus, the targeted entities are left with little or no defense against these exploits. What type of attack is outlined in the scenario?
- Watering Hole Attack
- Heartbleed Attack
- Shellshock Attack
- Spear Phising Attack
Answer: A
Q175 - Nedved is an IT Security Manager of a bank in his country. One day. he found out that there is a security breach to his company's email server based on analysis of a suspicious connection from the email server to an unknown IP Address. What is the first thing that Nedved needs to do before contacting the incident response team?
- Leave it as it Is and contact the incident response te3m right away
- Block the connection to the suspicious IP Address from the firewall
- Disconnect the email server from the network
- Migrate the connection to the backup email server
Answer: C
Q176 - A tester has been using the msadc.pl attack script to execute arbitrary commands on a Windows NT4 web server. While it is effective, the tester finds it tedious to perform extended functions. On further research, the tester come across a perl script that runs the following msadc functions:
Which exploit is indicated by this script?
- A buffer overflow exploit
- A chained exploit
- A SQL injection exploit
- A denial of service exploit
Answer: B
Q177 - From the two screenshots below, which of the following is occurring?
- 10.0.0.253 is performing an IP scan against 10.0.0.0/24, 10.0.0.252 is performing a port scan against 10.0.0.2.
- 10.0.0.253 is performing an IP scan against 10.0.0.2, 10.0.0.252 is performing a port scan against 10.0.0.2.
- 10.0.0.2 is performing an IP scan against 10.0.0.0/24, 10.0.0.252 is performing a port scan against 10.0.0.2.
- 10.0.0.252 is performing an IP scan against 10.0.0.2, 10.0.0.252 is performing a port scan against 10.0.0.2.
Answer: A
Q178 - What tool can crack Windows SMB passwords simply by listening to network traffic?
- This is not possible
- Netbus
- NTFSDOS
- L0phtcrack
Answer: D
Q179 - What is the difference between the AES and RSA algorithms?
- Both are asymmetric algorithms, but RSA uses 1024-bit keys.
- RSA is asymmetric, which is used to create a public/private key pair; AES is symmetric, which is used to encrypt data.
- Both are symmetric algorithms, but AES uses 256-bit keys.
- AES is asymmetric, which is used to create a public/private key pair; RSA is symmetric, which is used to encrypt data.
Answer: B
Q180 - What port number is used by LDAP protocol?
- 110
- 389
- 464
- 445
Answer: B