In today’s world, where nothing is impossible, how intercepting text messages can be? Yes, you have heard, right. It is possible to even without having the target phone. For this very purpose, you need a reliable spying application.
It is instead assumed to be a difficult task when it comes to finding a dependable application. Especially when you are unknown to hacking, spying, and such stuff, but over here, you will be made familiar with a strong text message interceptor. Stay with us so that you don’t miss any information.
Spyier a key to intercepting text messages
Whatever kind of spying errands you have, Spyier is the tool that is trustable without any second thoughts. It gives the high performance of all with the tools which other applications have failed to provide.
It has edge-cutting technology, which enables the users to monitor the target device without rooting or jailbreaking, which are themselves difficult to proceed with and are a sort of software hacking that can’t be quickly done by some common man.
Convenience of clients
Spyier is determined to help the people. As a result, it has the most straightforward commands to follow and is famous for its ease of usage. It can even be used by a beginner very quickly. No kind of technical knowledge is required to proceed with it.
It proceeds via remote processing so that there is not a chance to be caught. The client doesn’t have to get access to the target device physically. You can do everything distantly from a protected space without contacting the target device or introducing anything on it.
Privacy
Its main priority is to keep the privacy of its users intact. In such a case, it works in stealth mode and makes sure the user’s spying work is 100% safe and secure. You can read this article to learn about this application or can visit the official website of Spyier.
Using Spyier, you can not only intercept text messages, but you can keep an eye on the deleted text messages as well, call logs, contacts saved, the most frequently called number, and all such things. Spyier keeps data of all such things and the related ones likewise.
It also allows the user to see the social media activities of the target device. What kind of content the target device is receiving, sending, saving, etc. The perk over here is that the user can even access the deleted content whenever he wants to.
User friendly
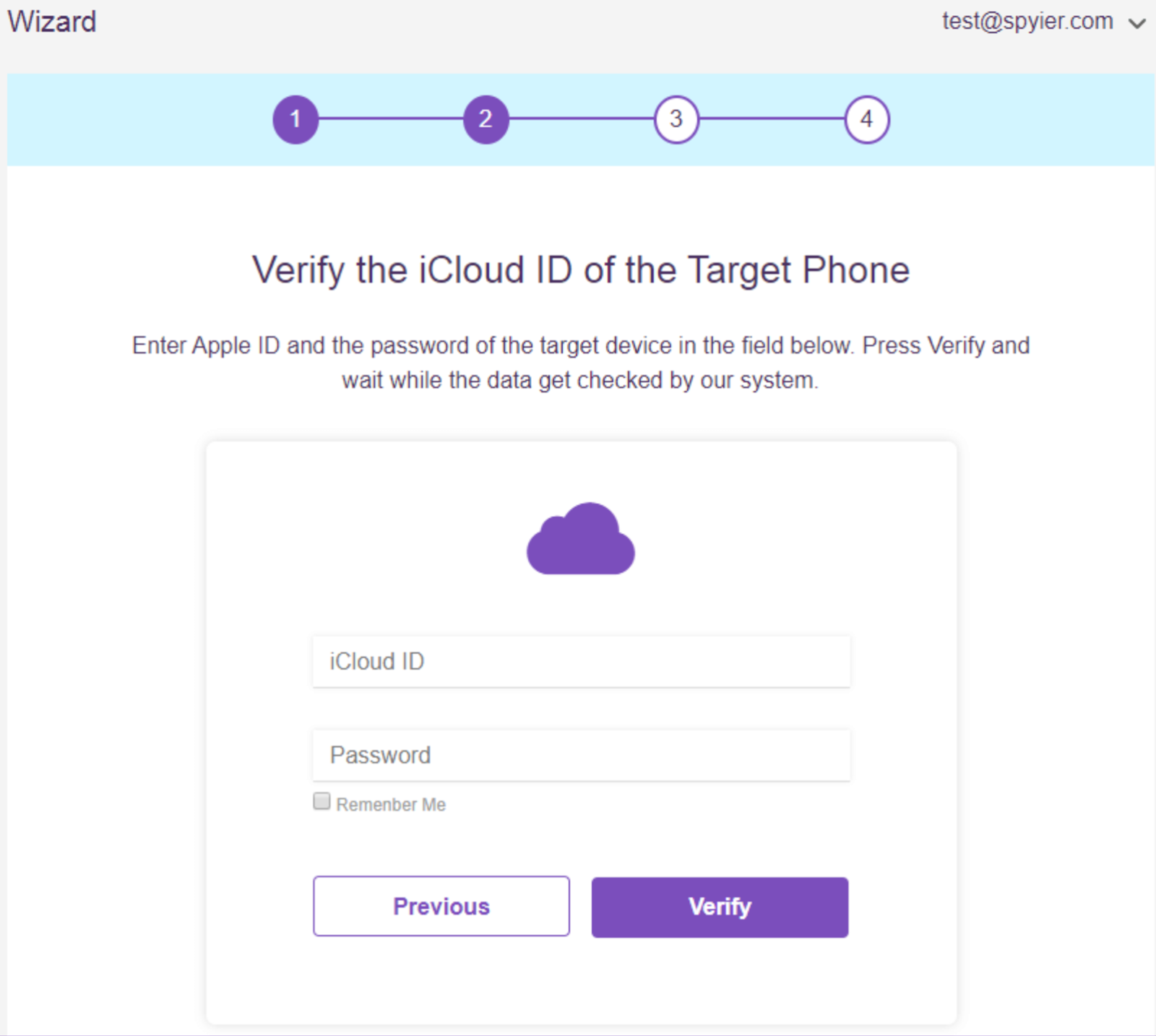
The application works for both operating systems such that IOS and Android. For the IOS system, you will have to provide the iCloud details of the target device. Once you are done providing the details, you will have to wait till all the data is synced and the rest of the work is of the application itself.
For the latter, you will have to install the application on the target device and then allow it to run in the background. The icon is easily removed from the screen after its installation, and it runs smoothly in the background.
Spyier is minimal in size and doesn’t occupy a large space on the device. Also, it doesn’t drain much of the battery and spares it for the usage of other applications. As a result, it is totally safe and secured to be utilized.
Free trial and live demo
For the convenience of the people, Spyier has a live demo on its official site so that people can watch that make up their mind about the application. So that when they start using it, there won’t be any doubts regarding the usage.
Additionally, it has a free trial for a month, so all the questions would be cleared. Individuals can utilize it without paying any money. Not all the administrations are provided in the trial, yet those which are incorporated give the full picture of what the application is about and how they might use it.
Keylogger
Spyier outfits its users with a feature that can determine the taps and keystrokes made on the target device. It makes sure that the user doesn’t miss any single activity happening on the target device. There is not a single thing that this application can’t uncover for you.
Whatever the target device user will share, get, and send on the cellphone will be recorded, and you will become more acquainted with pretty much all the exercises related to the target device.
Indeed, it will even uncover the passwords of social media accounts and other essential data. You can likewise see deleted data, so what else is undercover as there is everything before you.
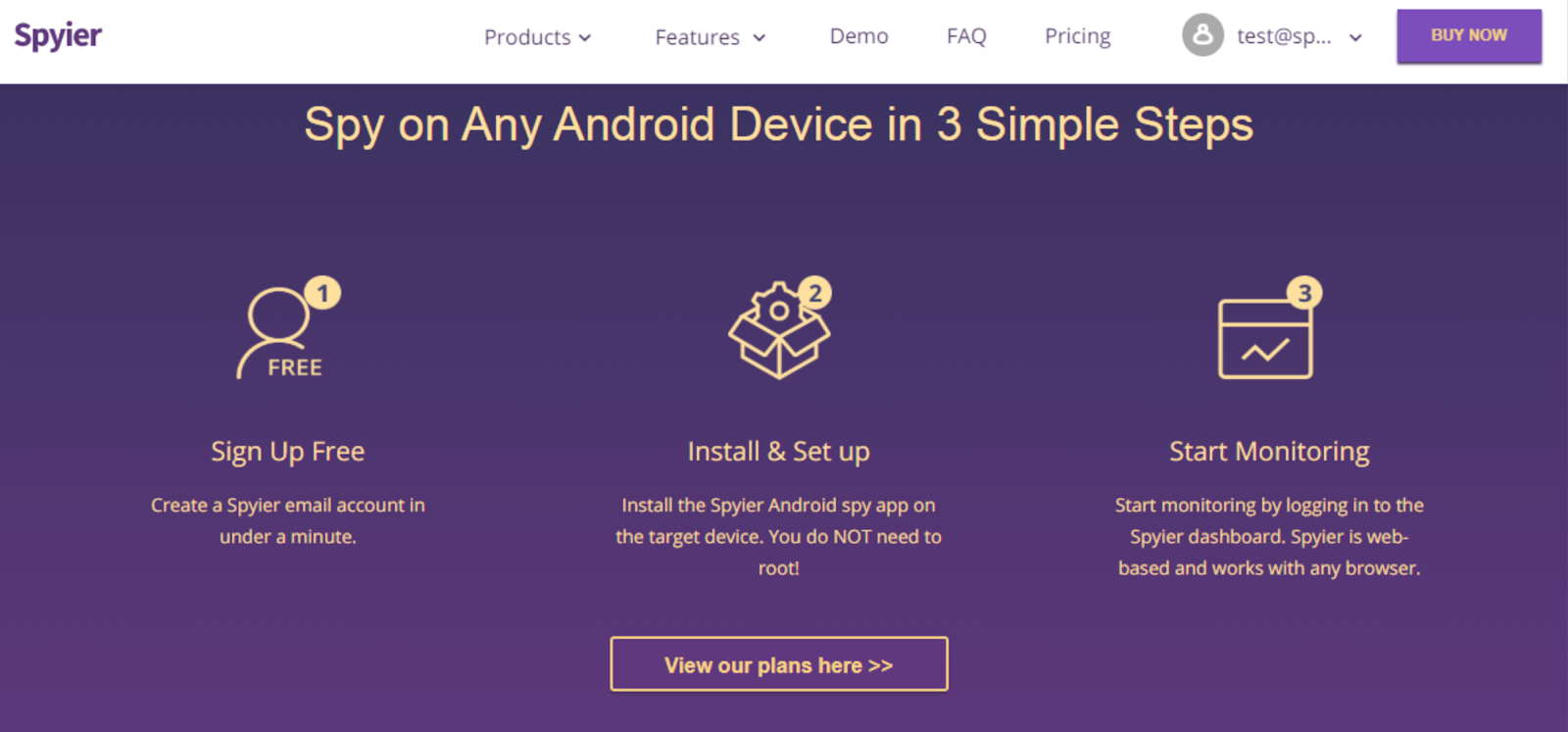
How to intercept text messages by Spyier
By following the following steps, you will be acquainted with how to do so.
Step 1.
As a matter of fact, the very first step is to create an account at the official site of Spyier. There you will have to provide some necessary data and the email address which you are currently using. Don’t forget to remember the password not to face any issue while logging in again.
Step 2.
Now you will be asked to choose the subscription plan and pick the operating system on which you will intercept text messages. If it is IOS, just provide the ICloud details, but you will have to download the application if it is Android.
Step 3.
Now you will have to give the ICloud details that come on the screen of the iPhone. This process will be somehow time taking it will be directly proportional to the amount of data you are about to draw. As a result, You will have to wait till the app is synced with the device.
Step 4.
In the case of Android, when the Spyier application is installed, you have to log in on the dashboard from your smartphone or pc or whatever thing you are using. The dashboard gives you a review of the activity of the device. From here, you can begin intercepting the text messages or utilize the application for different purposes.
Conclusion
This article will be sufficient for you to become more acquainted with the application and every feature and service it furnishes with. We can guarantee you that Spyier would be an extraordinary decision in the event that you need to intercept text messages without a target phone.
On the off chance that you actually have any inquiries, you can get in touch with us or go to the application’s official site and contact the client service group. They work every minute of every day and will manage you till the end, so you can resolve the issue you are going through.