The Yuki Chan is an Automated Penetration Testing tool through which you can easily audit any website and gather all possible information like website enumeration, ssl security auditing etc.
Features –
- Fully Automated Tool
- Intel-Gathering with smart search
- Complete Vulnerability Analysis
- Full Security Auditing
- Integration with OSINT Framework
- Tracking & System Enumeration Support
- Fuzzing Module
- Also supports CMS Auditing (like WPSCAN, JOOMSCAN etc)
- It also offers SSL Security Auditing
And here is the complete list of modules which Yuki-Chan supports:
- Whois domain analyzer
- Nslookup
- Nmap
- TheHarvester
- Metagoofil
- DNSRecon
- Sublist3r
- Wafw00f
- WAFNinja
- XSS Scanner
- WhatWeb
- Spaghetti
- WPscan
- WPscanner
- WPSeku
- Droopescan ( CMS Vulnerability Scanner WordPress, Joomla, Silverstripe, Drupal, And Moodle)
- SSLScan
- SSLyze
- A2SV
- Dirsearch
Installation of Yuki Chan in Kali Linux 2017.2
Before to start the installation of Yuki Chan, make sure that your Kali Linux machine must have these tools installed:
Nmap, Wafw00f, WPScan, SSLScan, SSLyze.
After the complete installation of above tools, you can proceed with the installation of Yuki Chan and for installation of Yuki-Chan, we’ll use Git Clone method:
Command: git clone https://github.com/Yukinoshita47/Yuki-Chan-The-Auto-Pentest.git

In next step, we need to give 777 permission to below files and directories:
chmod 777 wafninja joomscan install-perl-module.sh yuki.sh
chmod 777 Module/WhatWeb/whatweb
And after that you need to install a python module by typing “pip install -r requirements.txt”

To run Yuki Chan tool, type “./yuki.sh” in same terminal which shows you a welcome screen.

Now enter any domain which you want to pentest or scan.
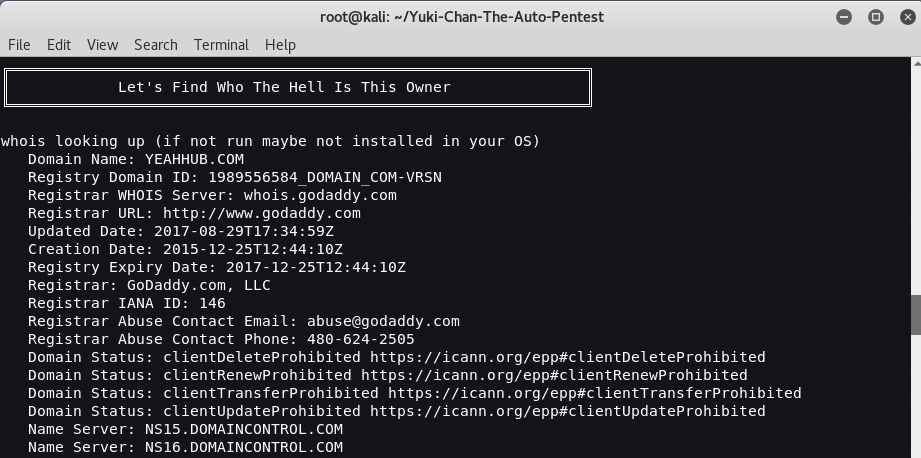
[#] Open Port information:

[#] TheHarvester Module

[#] Metagoofil Module

[#] Sublist3r Module

[#] WafW00f Module

[#] XSS Scanner Module

[#] WPScan Module
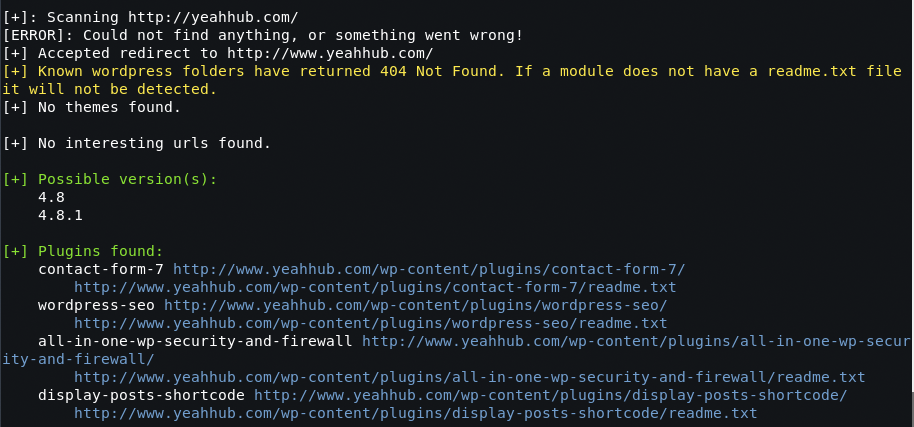
[#] WPSeku Module










but where it saves the output?