XML-RPC is a remote procedure call which uses XML to to encode its calls and HTTP as a transport mechanism. XML-RPC can be called as a system which enable user to publish post…
Read more
These days, everyone has a good reason to have a website. It’s not just large companies anymore. Individuals, families, and small or independent businesses all need to have one. Some individuals and small businesses don’t…
Read more
A media access control address (MAC address) of a device is a unique identifier assigned to a network interface controller (NIC) for communications at the data link layer of a network segment. MAC…
Read more
Typically, a Penetration Testing exercise is focused on identifying the gaps in security rather than harming a system. This is a key feature that separates a real attacker from an authorized Penetration Tester….
Read more
There are some great resources for analyzing your site’s speed such as Google’s PageSpeed Insights, Website Grader, and GTMetrix are the most popular. All services will analyze your site and tell you where…
Read more
Hacking the WordPress Core can make it very difficult to upgrade to the latest version of WordPress. Keeping WordPress current is an important step in overall web site security. If any security vulnerability is…
Read more
SQL injection is a technique, used to attack data-driven applications. Using this method, hackers will try to execute their SQL statements within your application and access your database data. Here is an example…
Read more
Malware is unfortunately far too common to ignore or be unaware of in this day and age. So this article should hopefully remedy some of the common questions. We guess the first one…
Read more
Enumeration is defined as the process of extracting user names, machine names, network resources, shares and services from a system. In this phase, the attacker creates an active connection to the system and…
Read more
Billu:B0x VM is created by one of the most popular Indian Ethical Hacker named as “Manish Kishan Tanwar” (a.k.a Indishell Hacker) who has created so many web shells in PHP language hosted at…
Read more
PHP is a general-purpose scripting language especially suited for Web development. It is open-source and can be deployed on all major operating systems and web servers free of charge. It is imperative, reflective and…
Read more
1. What are the two types of paper feeder mechanisms? A. Continuous tractor feed B. Continuous form feed C. Friction feed D. Injected 2. What type of printer is most likely to use…
Read more
Being as popular cms, it is no surprise that WordPress is often always under attack. Some 70% of Techno’s top 100 blogs are using WordPress as a Content Management System. XML-RPC on WordPress…
Read more
Many aspects of our lives rely on the Internet and computers, including communications (email, cell phones, texting), transportation (traffic control signals, car engine systems, airplane navigation), government (birth/death records, social security, licensing, tax…
Read more
Error reporting is a good thing, right? It gives you valuable insight into why your application failed. It gives you useful information such as what happened and where it happened. This information is…
Read more
Computer Networking Questions which we mentioned here in below article will definitely helps you to crack all kind of technical Interviews. Question 1: What is an Internet service provider? Answer: Internet service providers…
Read more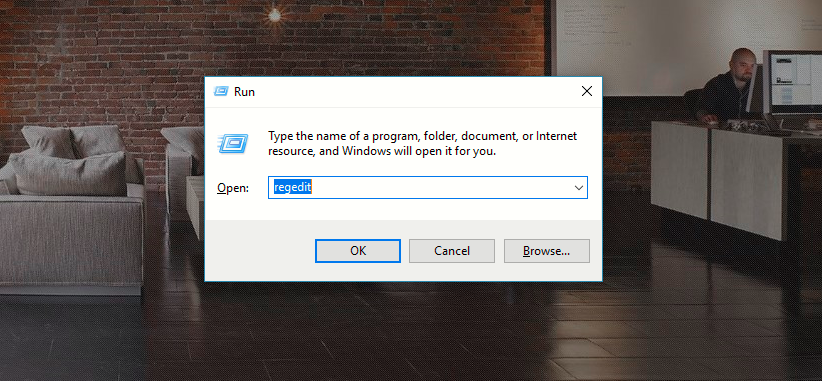
The Windows Registry is a database where all the information about a computer is stored. The Registry is used to store: Operating system configuration Application configuration information Hardware configuration information User security information Current…
Read more
File systems in the UNIX family have never been very well organized. Various incompatible naming conventions are used simultaneously, and different types of files are scattered randomly around the namespace. In many cases,…
Read more