
Exploit-DB is one of the most popular platform for their collection of exploits and whitepapers related to Linux/Windows/Assembly/Web/DOS etc.
Exploit-DB is the ultimate archive of exploits, shellcode, and security whitepapers. You can easily find the latest exploits related to Remote exploits, Web Application exploits, Local and Privilege Escalation exploits, Denial of Service exploits and shellcode exploits.
Now they have had their archive collection for some time and the Searchsploit bash script works just fine in this case.
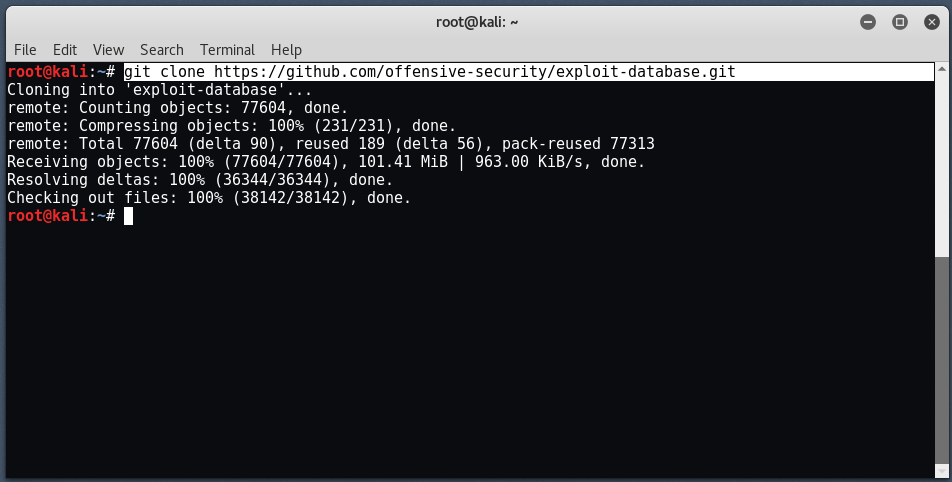
To install searchsploit, you can git clone method which directly clones the searchsploit into your Kali Linux OS from Github repository.
git clone https://github.com/offensive-security/exploit-database.git
To update, you can simply use git pull
If you are using the standard GNOME build of Kali Linux, the “exploitdb” package is already included by default!
Command: apt update && apt -y install exploitdb
If you are not using Kali Linux, the exploitdb package may not be available through the package manager in which case, you can continue to install the searchsploit package using above git command.
So, Searchsploit is an offline tool, where you can easily search all kind of exploits in offline mode.
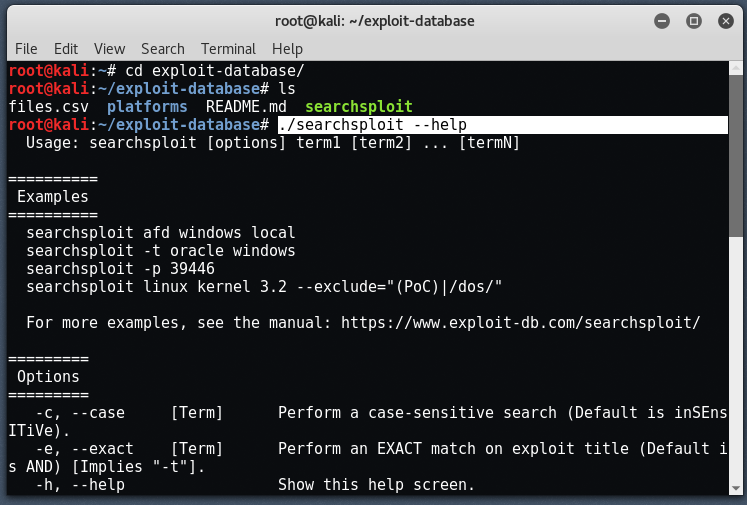
By using –help, you can easily see all the features and options which are available to you:
Usage: To search the exploits of Linux Kernel 3.2, you can simply type this command:
Command: searchsploit linux kernel 3.2
It will list all the exploits related to Linux Kernel along with the path of every exploit where its stored.

For exploits related to Apache 2.x, you can simply type “searchsploit Apache 2.x”

If you want to see the online URL of every exploit, then you can include the attribute (-w):
Command: searchsploit -w apache 2.x

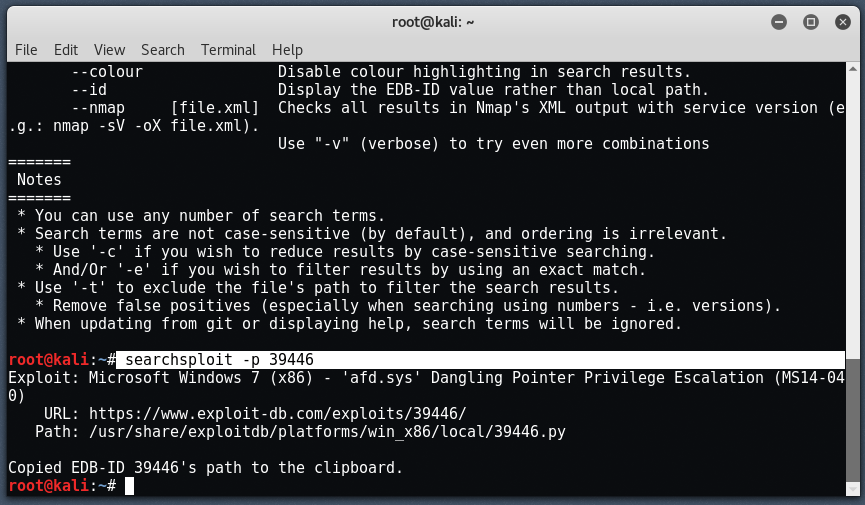
You can also include (-p) option to see the full relative path of the exploit.
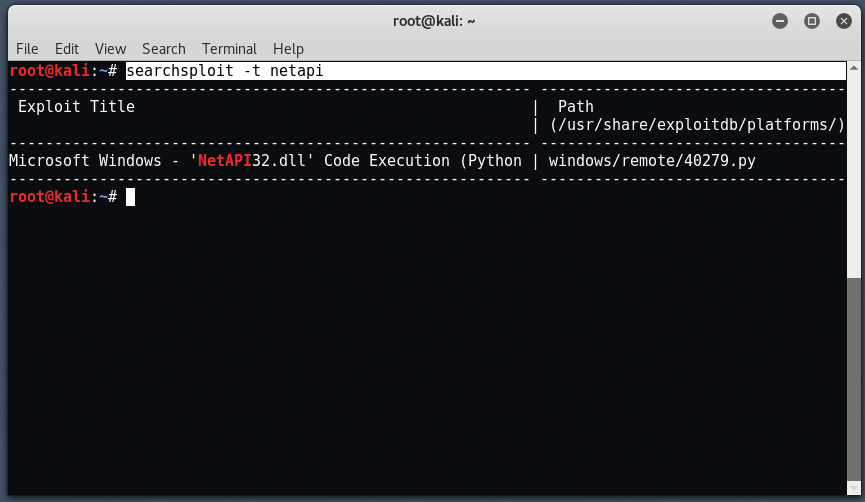
To search with (-t) option, will result the exploits which matches the title.
To update searchsploit, you can simply type “searchsploit -u”

If you need all the results in JSON format, then you simply add the attribute (-j):

For more info about Searchsploit, please refer to this link – https://www.exploit-db.com/searchsploit/








