
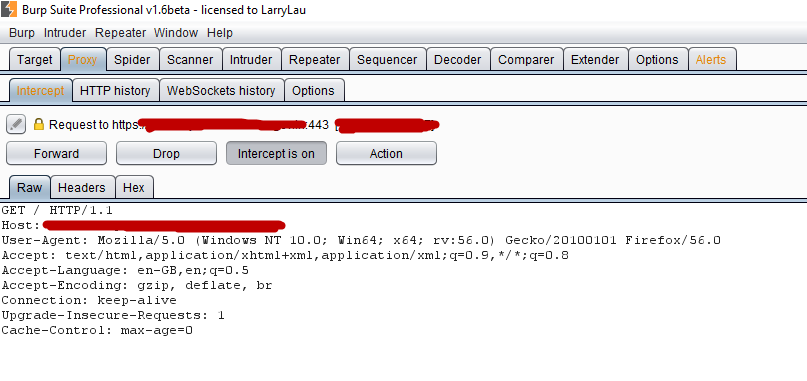
Web Application Proxies like Burp Proxy, WebScarab or Tamper Data Addon allow a security tester to intercept the requests/responses between the client HTTP application and the web server.
Proxies are the fundamental for the analysis of the web application. Portswigger Burp Suite is a suite of tools that will let us test and inspect the target web application. Burp Proxy intercepts the requests coming from your browser letting you modify them before they are actually sent to the remote server.
You’ll be able to manually or automatically modify the header and the content of the request But sometimes you’ll face some SSL related errors like “handshake alert: unrecognized_name” for especially HTTPS websites.

This issue is due to an update in Java 7, where Server Name Indication (SNI) support was enabled by default. SNI is an extension of the TLS protocol. It indicates that which host name is being contacted by the browser at the beginning of the handshake process.
The following browsers do offer support for SNI:
- Internet Explorer 7 or higher, on Windows Vista or newer. Does not work on Windows XP and Internet Explorer 8
- Mozilla Firefox 2.0 or higher
- Opera 8.0 or higher (the TLS 1.1 protocol must be implemented)
- Opera Mobile, version must be at least 10.1 beta on Android
- Google Chrome (Windows Vista or newer, Windows XP requires Chrome 6 or higher, OS X 10.5.7 or newer requires Chrome 5.0.342.1 or higher)
- Konqueror/KDE 4.7 or higher
- MobileSafari for Apple iOS 4.0 or newer
- Android standard browser on Honeycomb (v3.x) or higher
- Windows Phone 7
- MicroB on Maemo
And here is the list of all servers which supports SNI
- Apache 2.2.12 or higher, must use mod_ssl
- Apache Traffic Server 3.2.0 or higher
- Cherokee, must have TLS support implemented
- All versions of lighttpd 1.4.x and 1.5.x with patch, or 1.4.24 or higher without patch
- Nginx with implemented OpenSSL with SNI support
- F5 Networks Local Traffic Manager, version 11.1 or higher
- G-WAN Web app. Server, must use OpenSSL with SNI support
- LiteSpeed 4.1 or higher
- Pound 2.6 or higher
- Apache Tomcat on Java 7 or higher
- Microsoft Internet Information Server IIS 8
- Saetta Web Server via OpenSSL
- Citrix NetScaler 9.2 or higher
- HAProxy 1.5 or higher
The workaround to fix this handshake alert error is to set jsse.enableSNIExtension to “false” with the help of below command.
Command: java -Djsse.enableSNIExtension=false -jar burpsuite.jar

By executing above command, now you can easily intercept the request for SSL websites.
However if your website uses SNI, then your app will not be able to connect.








