
Today we’ll discuss about some cool and unsaturated methods through which you can generate some cash. These methods wont make you rich in 1 hour and we don’t guarantee you will make crazy…
Read more
PHP Functions always plays an important role in programming while developing an application/site in PHP language. User Defined Functions A function is a block of code that needs to be used multiple times…
Read more
Here you’ll learn about PHP Control Structures like IF/Else Loop, While Loop, Switch Loop, For/Foreach Loop etc If Else Statements Conditional statements perform different things for different states. The if else statement runs…
Read more
In this tutorial, we’ll cover Arrays and its types which are Numeric Arrays, Multi-Dimensional Arrays and Associative Arrays. Numeric Arrays An array is a special type of variable that is capable of storing…
Read more
Here we’ll cover PHP Operators that are of various types like Arithmetic Operators, Assignment Operators, Logical Operators and Comparison Operators Arithmetic Operators Arithmetic operators work with numeric values to perform common arithmetic operations….
Read more
In this chapter, we’ll cover PHP Data types which are of many types as listed below – Data Types A data type is the type of information stored within a variable. PHP has…
Read more
In this tutorial, you’ll learn about PHP Variables, Constants and Parameters. Regular Variables Variables are containers which we use for storing information. PHP variables work a bit differently to other languages so I…
Read more
PHP: Hypertext Preprocessor (PHP) is a free, open source, scripting language that is made primarily for the creation of dynamic websites. It is compatible with almost all modern servers and PHP scripts are…
Read more
Everyone wants to earn money online but some of them only gets success so this guide will helps you to decide which method is legit and which method is fake. 1) PTC Sites…
Read more
Today we’ll show you a list of up to 50+ Fiverr Gigs that you can start selling right now. Fiverr allows for 20 gigs per account, and a lot of users only create…
Read more
Client Side – Static and Dynamic analysis Test Name Description Tool OWASP Applicable Platform Result Reverse Engineering the Application Code Disassembling and Decompiling the application, Obfuscation checking apktool, dex2jar, Clutch, Classdump M10 All…
Read more
Hello, we’ve recently been hearing a lot of people wondering which VPN is the best for keeping your information safe. We have personally compiled the complete list of necessities for when you’re picking…
Read more
If you are using some JS based drop-down menus, then make sure that you must include that text links somewhere on page so that spiders will crawl your links easily. As you all…
Read more
Doxing, is the term used for the process of gathering personal information on a slave/target, although this does commonly take place over the internet, this isn’t always the case. There are many methods…
Read more
Today we’ll discuss about the hijack method used in banking sector i.e. botnets to steal money or some sensitive information from the user. What are these botnets used for? They are used for…
Read more
The average personal computer is a security nightmare, but what if i were to tell you there was a way around this, a way to make windows secure? VPNs, proxies and TOR only…
Read more
Yes, 1$ .com domain offer is now back and the best thing is you can book as many domains you want to book with single account. BookMyIdentity, an ICANN accredited domain registrar that…
Read more
For every businessman, development of website is much important as it acts as a most important promotional tool for his products and services. By Developing a website means, your website should be secured…
Read more
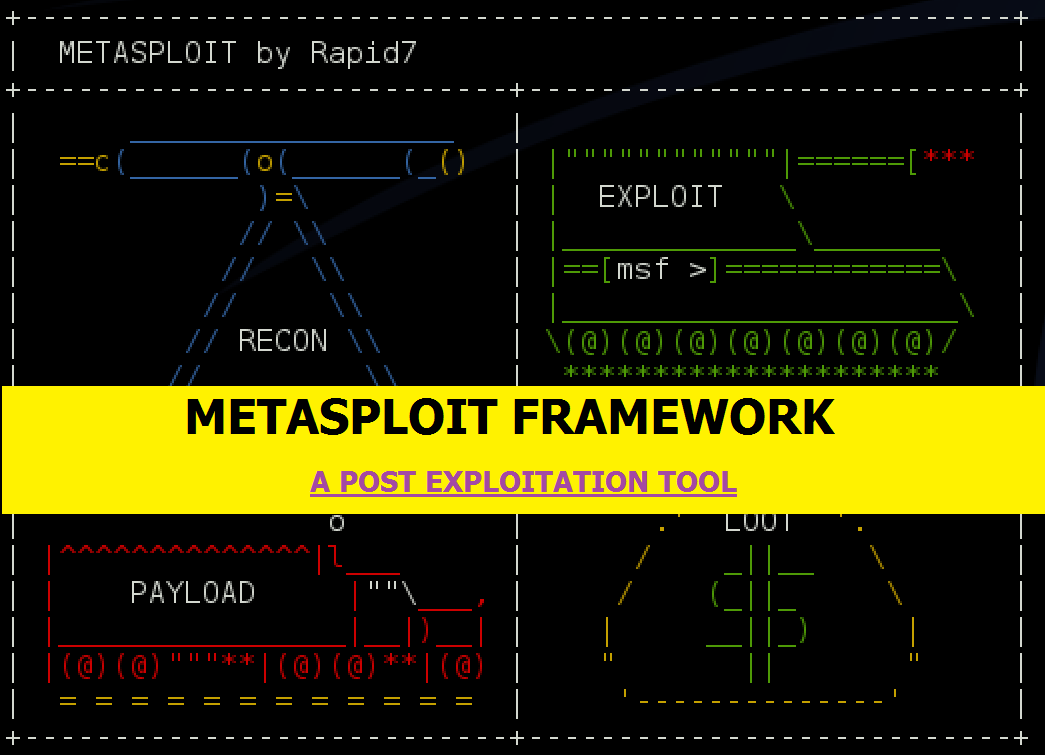
Penetration testing involves the use of a variety of manual and automated techniques to simulate an attack on an organization’s information security arrangements. One of the key points when managing testers is to…
Read more

Complete PHP Tutorial – Chapter 2
In previous chapter, you’ve learned about basics of PHP, Installation and XAMPP and in this tutorial we’ll cover PHP Tags & Comments. PHP Tags – All scripts start and end with these tags:…
Read more