Tor (www.torproject.org) is an open source implementation of the third generation onion routing that provides free access to an anonymous proxy network. Onion routing enables online anonymity by encrypting user traffic and then transmitting it through a series of onion routers.
At each router, a layer of encryption is removed to obtain routing information, and the message is then transmitted to the next node. It has been likened to the process of gradually peeling an onion, hence the name. It protects against traffic analysis attacks by guarding the source and destination of a user’s IP traffic.
To install Tor, perform the following steps:
1. Issue the apt-get update and apt-get upgrade commands,

and then use the following command:
Command: apt-get install tor

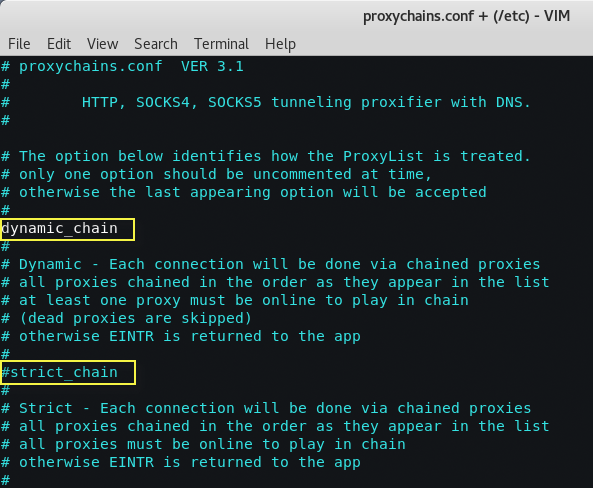
2. Once Tor is installed, edit the proxychains.conf file located in the /etc directory.
This file dictates the number and order of proxies that the test system will use on the way to the Tor network. proxy servers may be down, or they may be experiencing a heavy load (causing slow or latent connections); if this occurs, a defined or strict proxychain will fail because an expected link is missing.
Therefore, disable the use of (strict_chains) and enable (dynamic_chains), which ensures that the connection will be routed, as shown in the following screenshot:
3. Next, edit the [ProxyList] section to ensure that the socks5 proxy is present, as shown in the following screenshot:
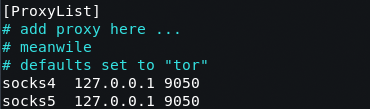
Open proxies can be easily found online and added to the proxychains file. Testers can take advantage of this to further obfuscate their identity.
For example, if there are reports that a certain country or block of IP addresses has been responsible for recent online attacks, look for open proxies from that location and add them to your list, or a separate configuration file.
4. To start the Tor service from a terminal window, enter the following command:
Command: service tor start
And to verify that Tor has started by using the following command:
Command: service tor status

5. It is important to verify that the Tor network is working and providing anonymous connectivity. Verify your source IP address first. From a terminal, enter the following command:
Command: proxychains iceweasel www.whatismyipaddress.com
You can also verify that Tor is functioning properly by accessing https://check.torproject.org.

Most command lines can be run from the console using proxychains to access the Tor network.
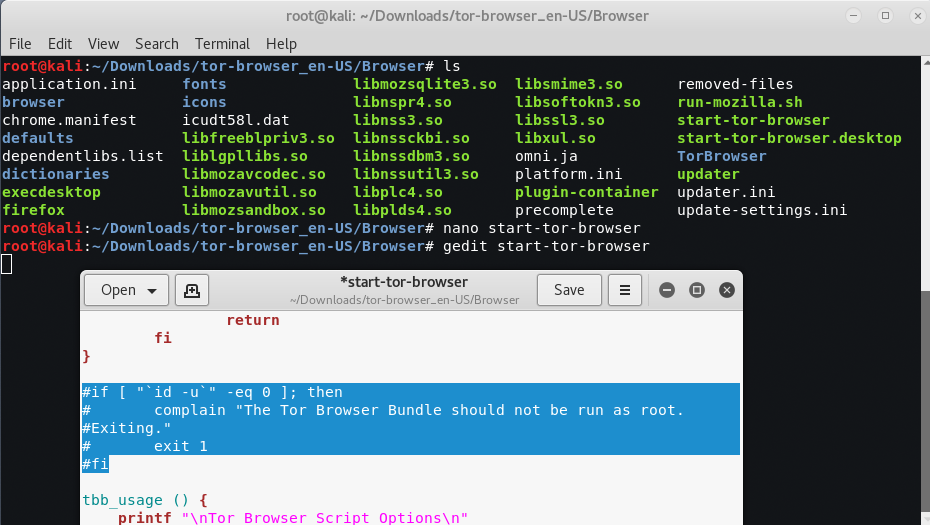
To download tor-bundle you need to download the package from their original website by clicking this link and extract the package by typing “tar -xvf tor*“.

Now to run tor-browser, you need to run a file which can be located at /root/Downloads/tor*/Browser/start-tor-browser But sometimes you’ll get an error like “The Tor Browser Bundle should not be run as root. Exiting.” as shown in below screenshot.

You can simply fix this issue by editing the same file i.e. “gedit start-tor-browser” and comment the below lines as shown in below screenshot.
# if [ “`id -u`” -eq 0 ]; then
# complain “The Tor Browser Bundle should not be run as root. Exiting.”
# exit 1
# fi
When using Tor, some considerations to be kept in mind are as follows:
- Tor provides an anonymizing service, but it does not guarantee privacy. Owners of the exit nodes are able to sniff traffic, and reportedly may be able to access user credentials.
- Vulnerabilities in the Tor Browser Bundle have reportedly been used by law enforcement to exploit systems and gain user information.
- ProxyChains does not handle UDP traffic.
- Some applications and services cannot run over this environment—in particular, Metasploit and nmap may break. The stealth SYN scan of nmap breaks out of proxychains and the connect scan is invoked instead; this can leak information to the target.
- Some browser applications (ActiveX, Adobe’s PDF applications, Flash, Java, RealPlay, and QuickTime) can be used to obtain your IP address.
- Ensure that you clear and block cookies before browsing.









Hmm. I have tried everything, made all of these changes as root. But when I click on //check.torproject.com I get this error from the tor website
Sorry. You are not using Tor.
along with my IP address…
Go to file manager/other locations/computer/etc /tor-browser/browser/start-tor-browser done now u r on tor
Or direct go to extracted folder of tor and the continue the above steps.