cURL is the magical utility that allows developers to download a URL’s content, explore response headers, get stock quotes, confirm our GZip encoding is working, and much more.
One more great usage of cURL for command line is POSTing form data to a server, especially while testing moderate to advanced form processing. And just like other cURL commands, POSTing form data is incredibly simple.
In order to use curl you will need some understanding of the HTTP protocol. If you’re unfamiliar with HTTP HEADERS, checkout All About HTTP Headers – a detailed guide.
Example 1 – If you simply want to make GET request with curl then the command is:
Command: curl https://www.yeahhub.com/
You can also send a POST request with curl as shown below:
Command: curl -X POST -F ‘username=yeahhub’ -F ‘password=yeahhub’ http://example.com/post.php

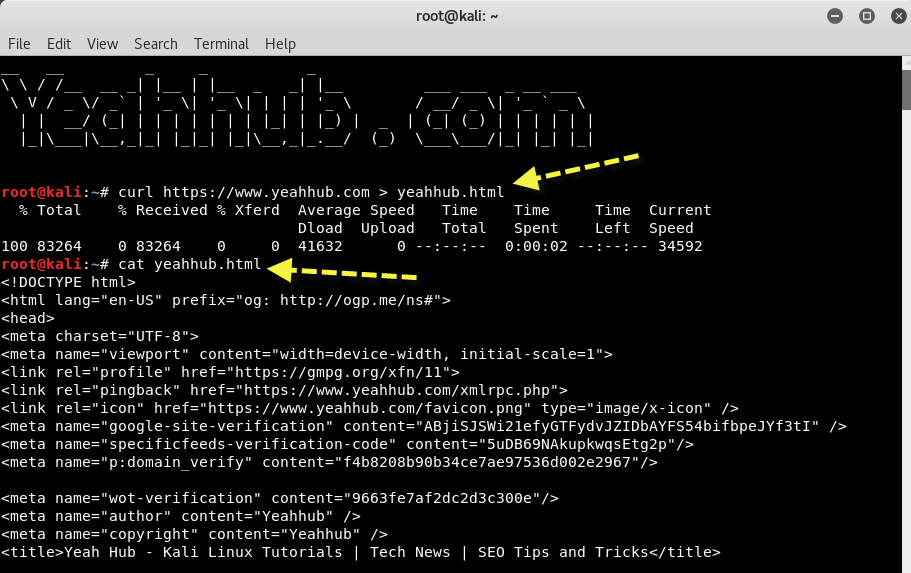
Example 2 – If you simply want to save whole response in an HTML file then the command is:
Command: curl https://www.yeahhub.com > filename.html
Example 3 – Furthermore, if you want to see the all the process of sending request and retrieving response in verbose mode, then you can use -v option as shown below:
Command: curl -v https://www.yeahhub.com/
The cURL verbose option includes both request headers and response headers. Lines starting with ‘>’ are the request headers or header data sent by curl.
Note: This option is always useful for debugging and seeing what’s going on “under the hood”.
With -V option (Capital V), you can check the basic information about curl like libcurl version and all.

Example 4 – You can also set a limit rate while sending the request to target.
Command: curl –limit-rate 2000B https://www.yeahhub.com/
The given speed is measured in bytes/second, unless a suffix is appended.
Limit rate is nothing but a maximum transfer rate which you an use for both upload and download. This feature is useful if you have a limited pipe and you’d like your transfer not to use your entire bandwidth.
Appending ‘k’ or ‘K’ will count the number as kilobytes, ‘m’ or ‘M’ makes it megabytes, while ‘g’ or ‘G’ makes it gigabytes. Examples: 200K, 3m and 1G.

Example 5 – cURL also supports both HTTP and SOCKS proxy servers, with optional authentication. It does not have special support for FTP proxy servers since there are no standards for those, but it can still be made to work with many of them. You can also use both HTTP and SOCKS proxies to transfer files to and from FTP servers.
You can even send the request directly to some interceptor (Burp Suite Tool) via –proxy option.
Command: curl –proxy 127.0.0.1:1337 yeahhub.com
If the proxy is specified with –proxy1.0 instead of –proxy or -x, then curl will use HTTP/1.0 instead of HTTP/1.1 for any CONNECT attempts.

Example 6 – You may specify any number of extra headers while making a request with curl.
Command: curl –header ‘Content-Type: application/json’ https://www.yeahhub.com/
Note that if you should add a custom header that has the same name as one of the internal ones curl would use, your externally set header will be used instead of the internal one.
This allows you to make even trickier stuff than curl would normally do. You should not replace internally set headers without knowing perfectly well what you’re doing.

Example 7 – You can even append your own custom header into response but for this you need to use -v option while making a request with cURL.
Command: curl –header ‘X-Header: Yeahhub’ -v https://www.yeahhub.com/

And in case, if you simply want to dump all the headers of a specific target then you can use the below command:
Command: curl –dump-header filename.txt yeahhub.com
Example 8 – Different protocols provide different ways of getting detailed information about specific files/documents. To get curl to show detailed information about a single file, you should use -I/–head option.
Command: curl –head https://www.yeahhub.com/

Example 9 – By default, every SSL connection curl makes is verified to be secure. The –insecure option allows curl to proceed and operate in insecure manner.
Command: curl –insecure https://www.yeahhub.com/

Example 10 – With the help of below command, SSL tells curl to use at least TLS version 1.x when negotiating with a remote TLS server. That means TLS version 1.0 or higher.
Command: curl –tlsv1 https://www.yeahhub.com/









