
For those who are interested in learning how to do Penetration Testing, there are many tools and operating systems are available, but very few targets to practice against safely – not to mention legally.
For many, learning penetration tactics has been through attacking systems on the Internet. While this might provide a wealth of opportunities and targets, it is also quite illegal. Many people have gone to jail, or paid huge amounts of money in fines and restitution all for hacking websites.
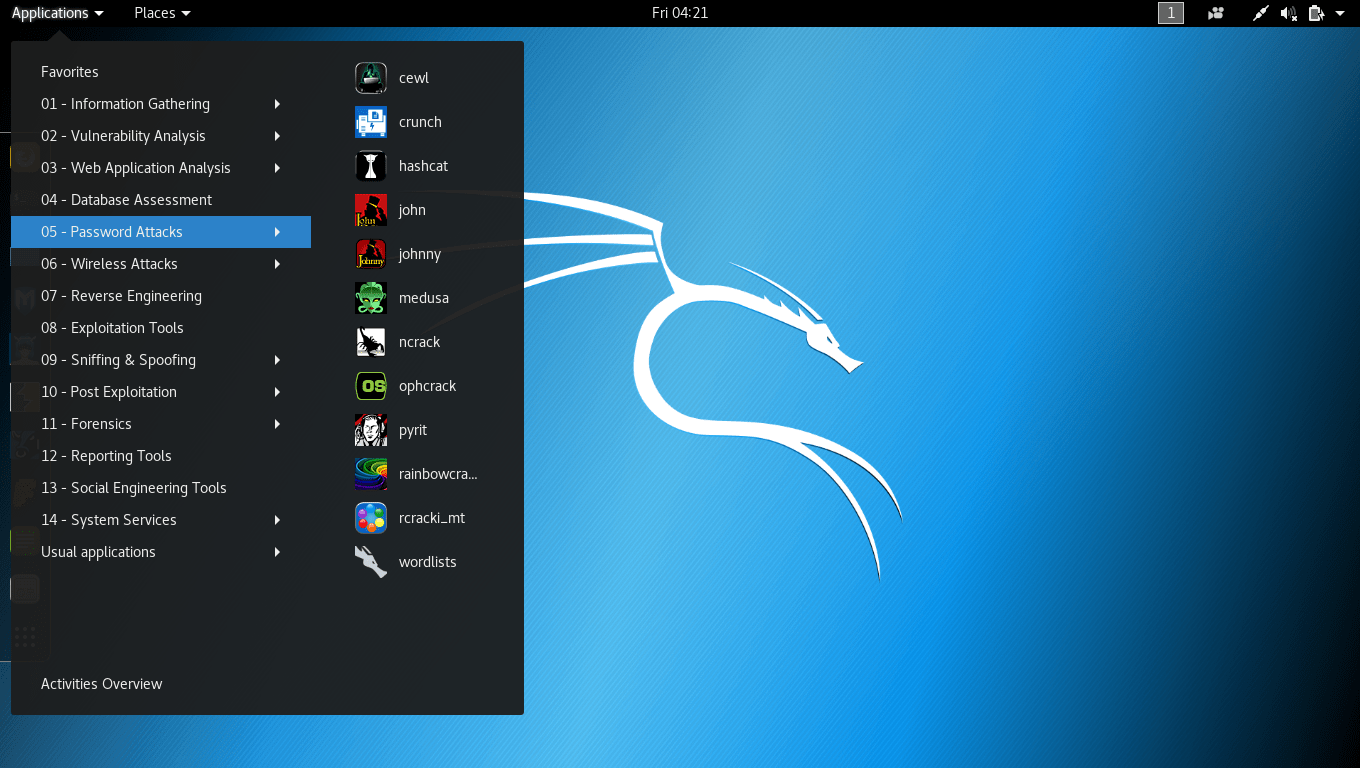
1. Kali Linux
Kali is the latest and greatest version of the ever popular Backtrack Linux penetration testing distribution. The creators of the Backtrack series kept Kali in a format very similar to Backtrack, so anyone familiar with the older Backtrack platform (BT-5r3) will feel right at home.
In latest version of Kali Linux, it has more than 600+ security testing tools which are already pre-installed in it.
Download Link – https://www.kali.org/downloads/
Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing. It is maintained and funded by Offensive Security Ltd. Mati Aharoni, Devon Kearns and Raphaël Hertzog are the core developers. – “Wikipedia”.
Kali Linux Version 1.0 was released on March 12, 2013. Five days later, Version 1.0.1 was released, which fixed the USB keyboard issue. In those five days, Kali has been downloaded more than 90,000 times.
The default Username of Kali Linux machine is “root” and Password is “toor“.
The following are the major features of Kali Linux –
- It is based on the Debian Linux distribution
- It has more than 600 penetration testing applications
- It has vast wireless card support
- It has a custom kernel patched for packet injection
- All Kali software packages are GPG signed by each developer
- Users can customize Kali Linux to suit their needs
- It supports ARM-based systems
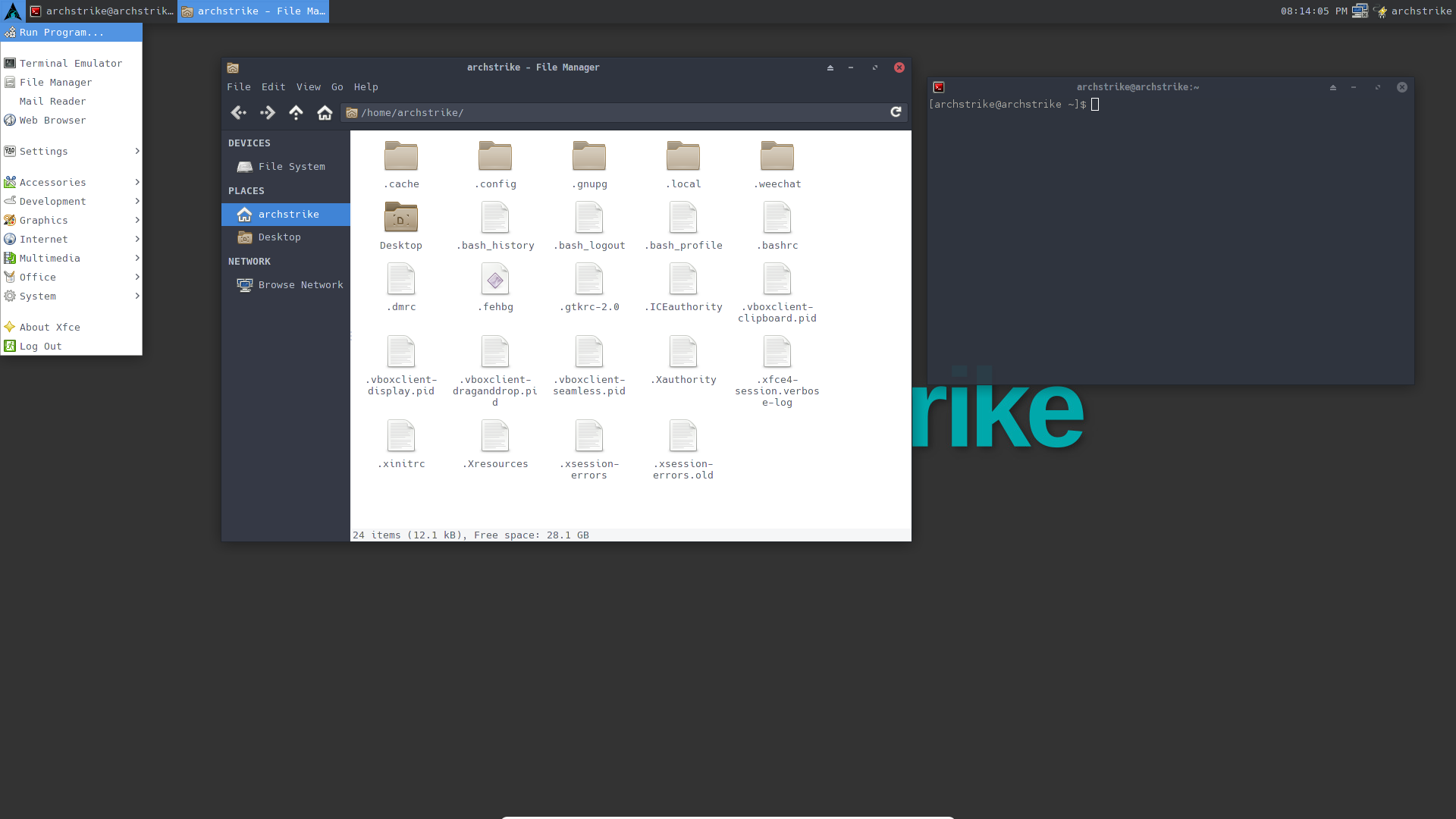
2. ArchStrike
ArchStrike is a penetration testing and security layer on top of Arch Linux. It follows the Arch Linux standards very closely in order to keep the packages clean, proper and easy to maintain.
An Arch Linux repository for security professionals and enthusiasts.
Download Link – https://archstrike.org/downloads
The default username and password for ArchStrike is “root” and for standard user, its “archstrike“.
For any kind of issues/questions/help, please visit official reddit link.
3. BlackArch
BlackArch Linux is an Arch Linux-based penetration testing distribution for penetration testers and security researchers. The repository contains over 1900 tools. You can even install tools individually or in groups. BlackArch Linux is also compatible with existing Arch installs.
Download Link – https://blackarch.org/downloads.html
According to Wikipedia – “BlackArch Linux is an Arch-derived Linux distribution designed for penetration testing and security research. It may be used as a standalone live CD or live USB, run from a virtual machine, or be installed to a computer’s hard disk. It is also possible to add its Arch Linux unofficial repo to an existing installation of Arch Linux.”

There are alot of pentesting tools included in this distribution, gathered under the BlackArch menu entry and organized in numerous categories, including anti-forensic, debuggers, crackers, decompilers, backdoors, fuzzers, keyloggers, proxy, spoofing, sniffers, malware, wireless and disassemblers.
4. Network Security Toolkit (NST)
Network Security Toolkit (NST) is a bootable ISO image based on Fedora 26 providing easy access to best-of-breed Open Source Network Security Applications and should run on mostly x86_64 systems.
The main intent of developing this toolkit was to provide the security professional and network administrator with a comprehensive set of Open Source Network Security Tools.
Download Link – http://www.networksecuritytoolkit.org/nst/index.html

The following are the major features of NST –
- Multi-Tap Network Packet Capture
- Web-Based Network Security Tools Management
- Host/IPv4 Address Geolocation
- Network/System Monitoring
- Network Intrusion Detection
- Network Interface Bandwidth Monitor
- Web-based Snort IDS Integration
- Active Connections Monitor
- Network Segment ARP Scanner
- Network Packet Capture CloudShark Upload Support
- Multi-Port Terminal Server
- VNC / RDP Desktop Session Management
5. BackBox
BackBox is more than an operating system, it is a Free Open Source Community project with the aim to promote the culture of security in IT environment and give its contribute to make it better and safer. All this using exclusively Free Open Source Software by demonstrating the potential and power of the community.
Download Link – https://backbox.org/download
BackBox comes up with 3 editions i.e. BackBox Linux, BackBox Cloud and BackBox Community.

The goal of this project is to raise security awareness, promoting initiatives such as public meetings, seminars and organizing practical workshops for Ethical Hackers.
More than 70+ Tools are already pre-installed in it like Metasploit Framework, Nmap, Beef, OpenVas, Ettercap, SET, Wireshark, Kismet, Aircrack and SQLMap.
6. Parrot
Parrot is a GNU/Linux distribution based on Debian and focused on Penetration Testing, Digital Forensics, Programming and Privacy protection. It includes a full portable laboratory for security and digital forensics experts, but it also includes all you need to develop your own software or protect your privacy while surfing the net.
Download Link – https://parrotsec.org/download.fx

The following are the major features of NST –
- Secure – Always updated, frequently released and fully sandboxed! Everything is under your complete control.
- Free (as in freedom) – Feel free to get the system, share with anyone, read the source code and change it as you want! this system is made to respect your freedom, and it ever will be.
- Lightweight – It is extremely lightweight and run surprisingly fast even on very old hardware or with very limited resources.
7. Buscador
Buscador is a Linux Virtual Machine that is pre-configured for online investigators. It was developed by David Westcott and Michael Bazzell, and distributions are maintained on this page.
Download Link – https://inteltechniques.com/buscador/

The current build is 3.5GB and includes the following resources: Custom Firefox Install and Add-Ons, Custom Chrome Install and Extensions, Tor Browser, Custom Video Manipulation Utilities, Custom Video Download Utility, Recon-NG, Maltego, Creepy, Metagoofil, MediaInfo, ExifTool, Spiderfoot, Google Earth Pro, EmailHarvester, theHarvester, Wayback Exporter, HTTrack Cloner, Web Snapper, Knock Pages, SubBrute, Twitter Exporter, Tinfoleak , InstaLooter, BleachBit, VeraCrypt and KeePass.
8. Fedora Security Lab
The Fedora Security Lab provides a safe test environment to work on security auditing, forensics, system rescue and teaching security testing methodologies in universities and other organizations.
Download Link – https://labs.fedoraproject.org/security/download/index.html
Fedora Security Lab is shipped as a live operating system. It’s everything you need to try out Fedora’s Security Lab – you don’t have to erase anything on your current system to try it out, and it won’t put your files at risk.

Featured Applications –
- Etherape – Etherape is a graphical network monitor for UNIX modeled after etherman. It displays network activity graphically.
- Ettercap – Ettercap is a comprehensive suite for man in the middle attacks.
- Medusa – Medusa is intended to be a speedy, massively parallel, modular, login brute-forcer.
- Scap-Workbench – A GUI tool that serves as an SCAP scanner and provides tailoring functionality for ?SCAP content.
- Nmap – Nmap is a free and open source utility for network discovery and security auditing.
- Skipfish – Skipfish is an active web application security reconnaissance tool.
- Wireshark – Wireshark is a network traffic analyzer for UNIX-ish operating systems.
- SQLninja – A tool targeted to test SQL Injection vulnerabilities on a web application using Microsoft® SQL Server as its back-end.
- Yersinia – Yersinia is a network tool designed to take advantage of some weakness in different network protocols
9. The Pentesters Framework
The PenTesters Framework (PTF) is a Python script designed for Debian/Ubuntu/ArchLinux based distributions to create a similar and familiar distribution for Penetration Testing.
Download Link – https://github.com/trustedsec/ptf
PTF attempts to install all of your penetration testing tools (latest and greatest), compile them, build them, and make it so that you can install/update your distribution on any machine. Everything is organized in a fashion that is cohesive to the Penetration Testing Execution Standard (PTES) and eliminates a lot of things that are hardly used.

PTF simplifies installation and packaging and creates an entire pentest framework for you. Since this is a framework, you can configure and add as you see fit.
10. AttifyOS
Distributions such as Kali Linux make it easier for us to carry out our penetration tests, vulnerability assessments, digital forensics gigs and wireless assessments. However, there are very few tools on such distributions that help you test the security of Internet of Things (IoT) devices as it needs bit of a customization. We now have AttifyOS to fill in the gap and help us test IoT security.
Download Link – https://github.com/adi0x90/attifyos

Attify OS is only meant for pentesting IoT devices. Instead of spending time installing, configuring and setting up various tools required for IoT pentesting, here is a pre-made distro for you containing the tools that would come handy during any Internet of Things Security Assessment or Penetration testing.








