Reverse-engineering is especially important with computer hardware and software. Programs are written in a language, say C, C++ or Java, that’s understandable by other programmers. But to run on a computer, they have to be translated by another program, called a compiler, into the ones and zeros of machine language. Compiled code is incomprehensible to most programmers, but there are ways to convert machine code back to a more human-friendly format, including a software tool called a decompiler.
Reverse-engineering is used for many purposes: as a learning tool; as a way to make new, compatible products that are cheaper than what’s currently on the market; for making software interoperate more effectively or to bridge data between different operating systems or databases; and to uncover the undocumented features of commercial products.
Reverse-engineering can also expose security flaws and questionable privacy practice.
With the help of Reverse Engineering we can modify a software at own way, Like we can change the name of Software, We can editing a software, We can convert Trial Software to License software n many more.
Below are listed best 5 Books of Reverse Engineering which are as follows:
1. Reverse Engineering for Beginners by Dennis Yurichev
The book is also known as RE4B. Written by Dennis Yurichev. Both English and Russian versions are available to download.
Dennis Yurichev has made this book free (libre), it is a contribution to the world of free knowledge and free education.
- Amazon Buy Link (Chinese Version) – https://www.amazon.cn/dp/B06XZ9JKH3
- Free Direct Download Link – https://beginners.re/

Topics which includes: Oracle RDBMS, Itanium, copy-protection dongles, LD_PRELOAD, stack overflow, ELF, win32 PE file format, x86-64, critical sections, syscalls, TLS, position-independent code (PIC), profile-guided optimization, C++ STL, OpenMP, win32 SEH.
2. Hacking the Xbox – An Introduction to Reverse Engineering by Andrew Huang, 2003
This hands-on guide to hacking begins with step-by-step tutorials on hardware modifications that teach basic hacking techniques as well as essential reverse engineering skills.
The book progresses into a discussion of the Xbox security mechanisms and other advanced hacking topics, with an emphasis on educating the readers on the important subjects of computer security and reverse engineering. Hacking the Xbox includes numerous practical guides, such as where to get hacking gear, soldering techniques, debugging tips and an Xbox hardware reference guide.
- Amazon Buy Link – https://www.amazon.com/Hacking-Xbox-Introduction-Reverse-Engineering/dp/1593270291
- NoStarch Link – https://nostarch.com/xbox.htm

This is a very interesting book about the original Xbox. It’s an engineer’s book written for engineers. This book describes in minute detail the trials, tribulations, failures, and success that the author had on two fronts.
3. The IDA Pro Book: The Unofficial Guide to the World’s Most Popular Disassembler by Chris Eagle, 2011
With IDA Pro, the interactive disassembler, you live in a source code-optional world. IDA can automatically analyze the millions of opcodes that make up an executable and present you with a disassembly. But at that point, your work is just beginning. With The IDA Pro Book, you’ll learn how to turn that mountain of mnemonics into something you can actually use.
- Amazon Buy Link – https://www.amazon.com/IDA-Pro-Book-Unofficial-Disassembler/dp/1593272898
- NoStarch Link – https://nostarch.com/idapro2.htm
Save time and effort as you learn to:
- Navigate, comment, and modify disassembly
- Identify known library routines, so you can focus your analysis on other areas of the code
- Use code graphing to quickly make sense of cross references and function calls
- Extend IDA to support new processors and filetypes using the SDK
- Explore popular plug-ins that make writing IDA scripts easier, allow collaborative reverse engineering, and much more
- Use IDA’s built-in debugger to tackle hostile and obfuscated code
IDA Pro is the world’s most popular disassembler. This book is for you if you are a beginner or intermediate reverser and you do not already own the first edition of The IDA Pro Book. Much of the second edition is similar, or identical in some places, to the first edition. The IDA Pro Book 2nd Edition does a great job using IDA Pro as the enabling tool for discussing specific techniques of reverse engineering. It is more of a book about reverse engineering rather than a user manual for IDA.
4. Practical Reverse Engineering: x86, x64, ARM, Windows Kernel, Reversing Tools, and Obfuscation by Bruce Dang, 2014
Practical Reverse Engineering goes under the hood of reverse engineering for security analysts, security engineers, and system programmers, so they can learn how to use these same processes to stop hackers in their tracks.
The book covers x86, x64, and ARM (the first book to cover all three); Windows kernel-mode code rootkits and drivers; virtual machine protection techniques; and much more. Best of all, it offers a systematic approach to the material, with plenty of hands-on exercises and real-world examples.
- Amazon Buy Link – https://www.amazon.com/Practical-Reverse-Engineering-Reversing-Obfuscation/dp/1118787315
Main Contents –
- Offers a systematic approach to understanding reverse engineering, with hands-on exercises and real-world examples
- Covers x86, x64, and advanced RISC machine (ARM) architectures as well as deobfuscation and virtual machine protection techniques
- Provides special coverage of Windows kernel-mode code (rootkits/drivers), a topic not often covered elsewhere, and explains how to analyze drivers step by step
- Demystifies topics that have a steep learning curve
- Includes a bonus chapter on reverse engineering tools
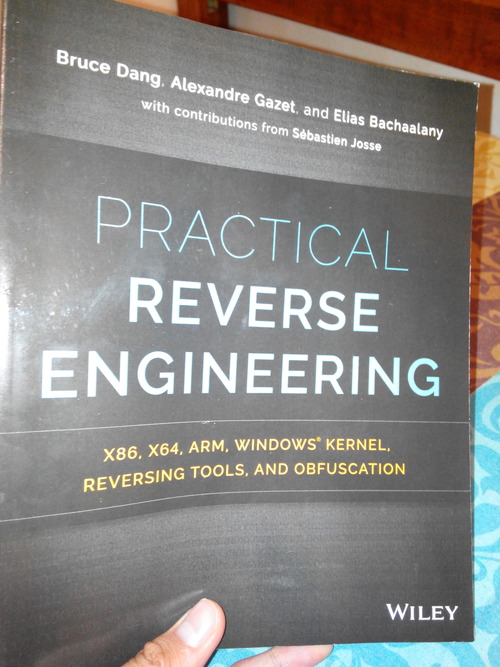
This book does a good job of teaching. It’s not just another reference book. A lot of technical books just blast facts at you, and sure you might learn a lot but you don’t know how the author learned those things himself. This book takes more of a teaching approach: You learn how the authors learned things. You need to have used IDA and windbg before you start reading this book.
It includes in-depth explanations and a lot of exercise which you wouldn’t see except in an expensive technical courses and in precious few of those. The book is well-written and highly readable, especially if you have a detailed technical bent.
5. Gray Hat Hacking The Ethical Hacker’s Handbook by Daniel Regalado, 5th Edition 2015
Gray Hat Hacking: The Ethical Hacker’s Handbook, Fifth Edition, clearly explains the enemy’s devious weapons, skills, and tactics and offers field-tested remedies, case studies, and interesting labs. You will get complete coverage of penetration testing, vulnerability discovery, malware analysis, reverse engineering, and Internet of Things security. State-of-the-art mobile exploits, ransomware, and legal issues are thoroughly explained.
Amazon Buy Link – https://www.amazon.com/Hacking-Ethical-Hackers-Handbook-Fifth/dp/1260108414