Microsoft Windows PowerShell is a great scripting platform for security researchers as well as for hackers. PowerShell is not only used to manage Windows OS, but Microsoft has also extended the capability of PowerShell script to Azure Cloud.
PowerShell not only helps in reducing the time it takes to perform the same tasks via GUI but also improves an organization’s overall security.
One of the logs that can trace an attacker’s activity is a transcript log. Transcript logs are basically an “over-the-shoulder” method of seeing what’s occurring in any given PowerShell session. It shows which commands the user is running and any output printed to the console.
By default, Windows PowerShell will record every transcript output to each users’ My Documents directory, with a file name that includes ‘PowerShell_transcript’, along with the computer name and time started.
The Start-Transcript and Stop-transcript cmdlets let you record all of your activities in the PowerShell console to a text file which allows you to review your entire PowerShell session but what if you want to save all transcription logs to a custom location?
In this article, we will provide you a step by step guide to enable the transcription logs of powershell with group policy editor.
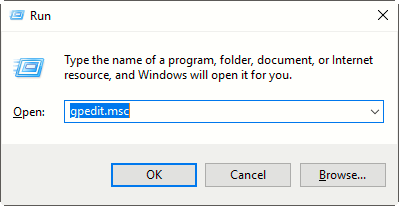
Step 1: Open Run Command and type “gpedit.msc” to open the Group Policy Editor.
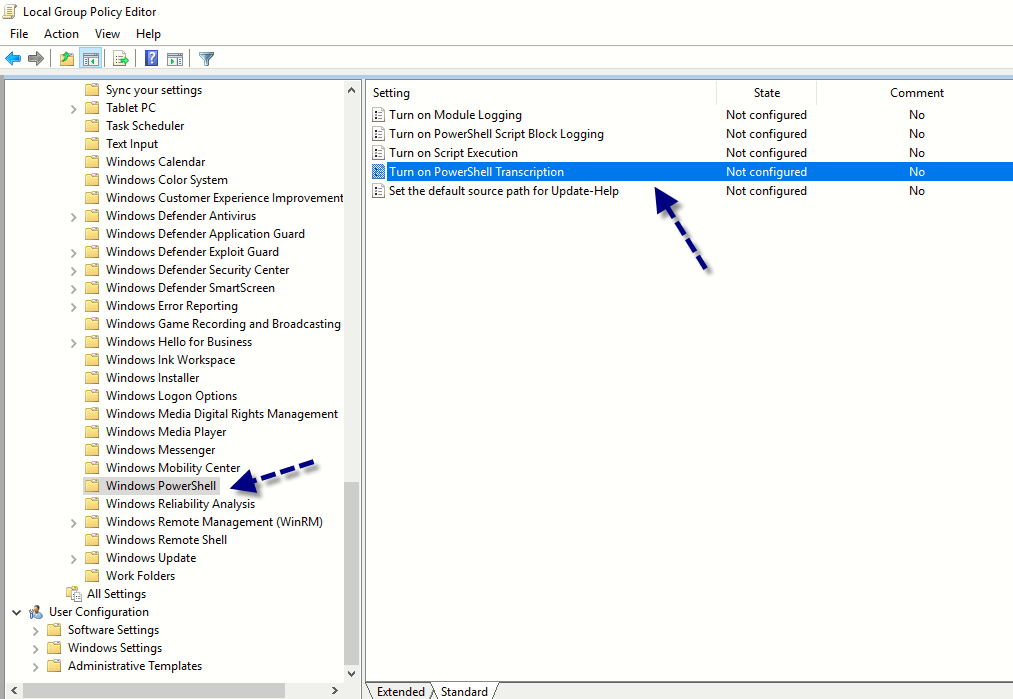
Step 2: Navigate to Computer Configuration -> Administrative Templates -> Windows Components -> Windows PowerShell.
Step 3: Furthermore, open Windows Powershell option and double click on “Turn on PowerShell Transcription” as shown below:
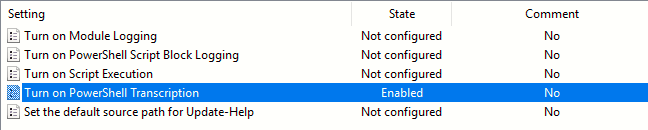
If you enable this policy setting, Windows PowerShell will enable transcripting for Windows PowerShell.
Step 4: To enable this setting, click on Enabled option and enter your preferred Output Directory (let’s for e.g. C:\PS_Logs).
The transcript file will now be created in the selected output directory i.e. C:\PS_Logs.
This policy setting lets you capture the input and output of Windows PowerShell commands into text-based transcripts.
Note: This policy setting exists under both Computer Configuration and User Configuration in the Group Policy Editor. The Computer Configuration policy setting takes precedence over the User Configuration policy setting.”
Step 5: Now we’re going to run a simple command of powershell which gives you basic system information about your OS.
Command: Get-CimInstance Win32_OperatingSystem | Select-Object Caption, InstallDate, ServicePackMajorVersion, OSArchitecture, BootDevice, BuildNumber, CSName | FL
Step 6: As soon as you run the above command in windows powershell, a same log file will be created under C:\PS_Logs directory with proper timestamp as shown below: