The Hacker’s Handbook is a non-fiction book from the 1980s effectively explaining how computer systems of the period were hacked. They actually explained the actual hacking attempts such as password hacking, brute forcing, ssh hacking etc. The very first edition was published in year 1985 by E. Arthur Brown.

Here is the complete collection of “The Hacker’s Handbook” which are as listed below:

1. The Database Hacker’s Handbook
- Buy Link (Paperback) – https://www.wiley.com/en-us/The+Database+Hacker%27s+Handbook%3A+Defending+Database+Servers-p-9780764578014
- Price – $50.00
- Publishing Month/Year – July 2015
- Authors – David Litchfield, Chris Anley, John Heasman, Bill Grindlay
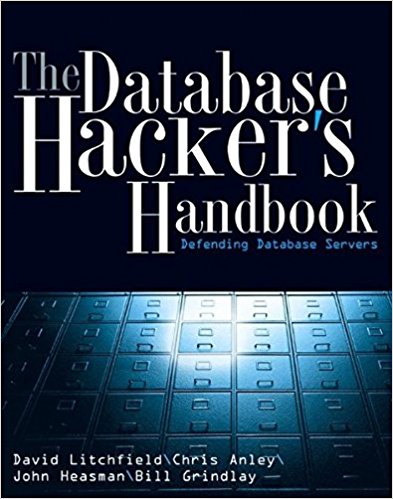
Databases are the nerve center of our economy. Every piece of your personal information is stored there-medical records, bank accounts, employment history, pensions, car registrations, even your children’s grades and what groceries you buy. Database attacks are potentially crippling-and relentless.
Contents –
- Chapter 1: Why Care About Database Security?
- Chapter 2: The Oracle Architecture.
- Chapter 3: Attacking Oracle.
- Chapter 4: Oracle: Moving Further into the Network.
- Chapter 5: Securing Oracle.
- Chapter 6: IBM DB2 Universal Database.
- Chapter 7: DB2: Discovery, Attack, and Defense.
- Chapter 8: Attacking DB2.
- Chapter 9: Securing DB2.
- Chapter 10: The Informix Architecture.
- Chapter 11: Informix: Discovery, Attack, and Defense.
- Chapter 12: Securing Informix.
- Chapter 13: Sybase Architecture.
- Chapter 14: Sybase: Discovery, Attack, and Defense.
- Chapter 15: Sybase: Moving Further into the Network.
- Chapter 16: Securing Sybase.
- Chapter 17: MySQL Architecture.
- Chapter 18: MySQL: Discovery, Attack, and Defense.
- Chapter 19: MySQL: Moving Further into the Network.
- Chapter 20: Securing MySQL.
- Chapter 21: Microsoft SQL Server Architecture.
- Chapter 22: SQL Server: Exploitation, Attack, and Defense.
- Chapter 23: Securing SQL Server.
- Chapter 24: The PostgreSQL Architecture.
- Chapter 25: PostgreSQL: Discovery and Attack.
- Chapter 26: Securing PostgreSQL.
2. The Shellcoder’s Handbook: Discovering and Exploiting Security Holes 2nd Edition
- Buy Link (Paperback) – https://www.wiley.com/en-us/The+Shellcoder%27s+Handbook%3A+Discovering+and+Exploiting+Security+Holes%2C+2nd+Edition-p-9780470080238
- Price – $49.99
- Publishing Month/Year – August 2007
- Authors – Chris Anley, John Heasman, Felix Lindner, Gerardo Richarte

The first edition of this volume attempted to show the reader how security vulnerabilities are discovered and exploited, and this edition holds fast to that same objective. This much-anticipated revision, written by the ultimate group of top security experts in the world, features 40% new content on how to find security holes in any operating system or application.
Contents –
- Chapter 1: Before You Begin
- Chapter 2: Stack Overflows.
- Chapter 3: Shellcode.
- Chapter 4: Introduction to Format String Bugs.
- Chapter 5: Introduction to Heap Overflows.
- Chapter 6: The Wild World of Windows.
- Chapter 7: Windows Shellcode.
- Chapter 8: Windows Overflows.
- Chapter 9: Overcoming Filters.
- Chapter 10: Introduction to Solaris Exploitation.
- Chapter 11: Advanced Solaris Exploitation.
- Chapter 12: OS X Shellcode.
- Chapter 13: Cisco IOS Exploitation.
- Chapter 14: Protection Mechanisms.
- Chapter 15: Establishing a Working Environment.
- Chapter 16: Fault Injection.
- Chapter 17: The Art of Fuzzing.
- Chapter 18: Source Code Auditing: Finding Vulnerabilities in C-Based Languages.
- Chapter 19: Instrumented Investigation: A Manual Approach.
- Chapter 20: Tracing for Vulnerabilities.
- Chapter 21: Binary Auditing: Hacking Closed Source Software.
- Chapter 22: Alternative Payload Strategies.
- Chapter 23: Writing Exploits that Work in the Wild.
- Chapter 24: Attacking Database Software.
- Chapter 25: Unix Kernel Overflows.
- Chapter 26: Exploiting Unix Kernel Vulnerabilities.
- Chapter 27: Hacking the Windows Kernel.
3. The Mac Hacker’s Handbook 1st Edition
- Buy Link (Paperback) – https://www.wiley.com/en-us/The+Mac+Hacker%27s+Handbook-p-9780470395363
- Price – $49.99
- Publishing Month/Year – March 2009
- Authors – Charlie Miller and Dino Dai Zovi

Beginning with the core differences between Mac OS X and Windows or Linux, this book follows the steps an attacker would take. You will learn the tools needed to find vulnerabilities, the techniques used to exploit them, and the means by which attackers maintain control once they gain access. When you know how they get in, you’ll know how to keep them out.
Contents –
- Chapter 1: Mac OS X Architecture.
- Chapter 2: Mac OS X Parlance.
- Chapter 3: Attack Surface.
- Chapter 4: Tracing and Debugging.
- Chapter 5: Finding Bugs.
- Chapter 6: Reverse Engineering.
- Chapter 7: Exploiting Stack Overflows.
- Chapter 8: Exploiting Heap Overflows.
- Chapter 9: Exploit Payloads.
- Chapter 10: Real-World Exploits.
- Chapter 11: Injecting, Hooking, and Swizzling.
- Chapter 12: Rootkits.
4. The Web Application Hacker’s Handbook: Finding and Exploiting Security Flaws, 2nd Edition
- Buy Link (Paperback) – https://www.wiley.com/en-us/The+Web+Application+Hacker%27s+Handbook%3A+Finding+and+Exploiting+Security+Flaws%2C+2nd+Edition-p-9781118026472
- Price – $50.00
- Publishing Month/Year – September 2011
- Authors – Dafydd Stuttard, Marcus Pinto

This practical book has been completely updated and revised to discuss the latest step-by-step techniques for attacking and defending the range of ever-evolving web applications. You’ll explore the various new technologies employed in web applications that have appeared since the first edition and review the new attack techniques that have been developed, particularly in relation to the client side.
Contents –
- Chapter 1: Web Application (In)security.
- Chapter 2: Core Defense Mechanisms.
- Chapter 3: Web Application Technologies.
- Chapter 4: Mapping the Application.
- Chapter 5: Bypassing Client-Side Controls.
- Chapter 6: Attacking Authentication.
- Chapter 7: Attacking Session Management.
- Chapter 8: Attacking Access Controls.
- Chapter 9: Attacking Data Stores.
- Chapter 10: Attacking Back-End Components.
- Chapter 11: Attacking Application Logic.
- Chapter 12: Attacking Users: Cross-Site Scripting.
- Chapter 13: Attacking Users: Other Techniques.
- Chapter 14: Automating Customized Attacks.
- Chapter 15: Exploiting Information Disclosure.
- Chapter 16: Attacking Native Compiled Applications.
- Chapter 17: Attacking Application Architecture.
- Chapter 18: Attacking the Application Server.
- Chapter 19: Finding Vulnerabilities in Source Code.
- Chapter 20: A Web Application Hacker’s Toolkit.
- Chapter 21: A Web Application Hacker’s Methodology.
5. iOS Hacker’s Handbook
- Buy Link (Paperback) – https://www.wiley.com/en-us/iOS+Hacker%27s+Handbook-p-9781118204122
- Price – $44.99
- Publishing Month/Year – May 2012
- Authors – Charlie Miller, Dion Blazakis, Dino DaiZovi, Stefan Esser, Vincenzo Iozzo, Ralf-Philip Weinmann

The book explains how the operating system works, its overall security architecture, and the security risks associated with it, as well as exploits, rootkits, and other payloads developed for it.
Contents –
- Chapter 1: iOS Security Basics.
- Chapter 2: iOS in the Enterprise.
- Chapter 3: Encryption.
- Chapter 4: Code Signing and Memory Protections.
- Chapter 5: Sandboxing.
- Chapter 6: Fuzzing iOS Applications.
- Chapter 7: Exploitation.
- Chapter 8: Return-Oriented Programming.
- Chapter 9: Kernel Debugging and Exploitation.
- Chapter 10: Jailbreaking.
- Chapter 11: Baseband Attacks.
6. Android Hacker’s Handbook
- Buy Link (Paperback) – https://www.wiley.com/en-us/Android+Hacker%27s+Handbook-p-9781118608647
- Price – $50.00
- Publishing Month/Year – March 2014
- Authors – Joshua J. Drake, Zach Lanier, Collin Mulliner, Pau Oliva Fora, Stephen A. Ridley, Georg Wicherski

Written by experts who rank among the world’s foremost Android security researchers, this book presents vulnerability discovery, analysis, and exploitation tools for the good guys. Following a detailed explanation of how the Android OS works and its overall security architecture, the authors examine how vulnerabilities can be discovered and exploits developed for various system components, preparing you to defend against them.
Contents –
- Chapter 1: Looking at the Ecosystem.
- Chapter 2: Android Security Design and Architecture.
- Chapter 3: Rooting Your Device.
- Chapter 4: Reviewing Application Security.
- Chapter 5: Understanding Android’s Attack Surface.
- Chapter 6: Finding Vulnerabilities with Fuzz Testing.
- Chapter 7: Debugging and Analyzing Vulnerabilities.
- Chapter 8: Exploiting User Space Software.
- Chapter 9: Return Oriented Programming.
- Chapter 10: Hacking and Attacking the Kernel.
- Chapter 11: Attacking the Radio Interface Layer.
- Chapter 12: Exploit Mitigations.
- Chapter 13: Hardware Attacks.
7. The Browser Hacker’s Handbook
- Buy Link (Paperback) – https://www.wiley.com/en-us/The+Browser+Hacker%27s+Handbook-p-9781118662090
- Price – $55.00
- Publishing Month/Year – March 2014
- Authors – Wade Alcorn, Christian Frichot, Michele Orru

The Browser Hacker’s Handbook gives a practical understanding of hacking the everyday web browser and using it as a beachhead to launch further attacks deep into corporate networks. Written by a team of highly experienced computer security experts, the handbook provides hands-on tutorials exploring a range of current attack methods.
Contents –
- Chapter 1: Web Browser Security.
- Chapter 2: Initiating Control.
- Chapter 3: Retaining Control.
- Chapter 4: Bypassing the Same Origin Policy.
- Chapter 5: Attacking Users.
- Chapter 6: Attacking Browsers.
- Chapter 7: Attacking Extensions.
- Chapter 8: Attacking Plugins.
- Chapter 9: Attacking Web Applications.
- Chapter 10: Attacking Networks.
- Chapter 11: Epilogue: Final Thoughts.
8. The Mobile Application Hacker’s Handbook
- Buy Link (Paperback) – https://www.wiley.com/en-us/The+Mobile+Application+Hacker%27s+Handbook-p-9781118958506
- Price – $60.00
- Publishing Month/Year – February 2015
- Authors – Dominic Chell, Tyrone Erasmus, Shaun Colley, Ollie Whitehouse

The Mobile Application Hacker’s Handbook is a comprehensive guide to securing all mobile applications by approaching the issue from a hacker’s point of view. Heavily practical, this book provides expert guidance toward discovering and exploiting flaws in mobile applications on the iOS, Android, Blackberry, and Windows Phone platforms.
Contents –
- Chapter 1: Mobile Application (In)security.
- Chapter 2: Analyzing iOS Applications.
- Chapter 3: Attacking iOS Applications.
- Chapter 4: Identifying iOS Implementation Insecurities.
- Chapter 5: Writing Secure iOS Applications.
- Chapter 6: Analyzing Android Applications.
- Chapter 7: Attacking Android Applications.
- Chapter 8: Identifying and Exploiting Android Implementation Issues.
- Chapter 9: Writing Secure Android Applications.
- Chapter 10: Analyzing Windows Phone Applications.
- Chapter 11: Attacking Windows Phone Applications.
- Chapter 12: Identifying Windows Phone Implementation Issues.
- Chapter 13: Writing Secure Windows Phone Applications.
- Chapter 14: Analyzing BlackBerry Applications.
- Chapter 15: Attacking BlackBerry Applications.
- Chapter 16: Identifying BlackBerry Application Issues.
- Chapter 17: Writing Secure BlackBerry Applications.
- Chapter 18: Cross Platform Mobile Applications.
9. Car Hacker’s Handbook
- Buy Link (Paperback) – https://nostarch.com/carhacking
- Price – $49.95
- Publishing Month/Year – March 2016
- Authors – Craig Smith

The Car Hacker’s Handbook will give you a deeper understanding of the computer systems and embedded software in modern Avehicles. It begins by examining vulnerabilities and providing detailed explanations of communications over the CAN bus and Abetween devices and systems.
Contents –
- Chapter 1: Understanding Threat Models
- Chapter 2: Bus Protocols
- Chapter 3: Vehicle Communication with SocketCAN
- Chapter 4: Diagnostics and Logging
- Chapter 5: Reverse Engineering the CAN Bus
- Chapter 6: ECU Hacking
- Chapter 7: Building and Using ECU Test Benches
- Chapter 8: Attacking ECUs and Other Embedded Systems
- Chapter 9: In-Vehicle Infotainment Systems
- Chapter 10: Vehicle-to-Vehicle Communication
- Chapter 11: Weaponizing CAN Findings
- Chapter 12: Attacking Wireless Systems with SDR
- Chapter 13: Performance Tuning