In the early 90’s GNU/Linux systems consisted of little more than a beta – quality Linux kernel and a small collection of software ported from the GNU project. It was a true hacker’s…
Read more
Windows Defender Security Intelligence (WDSI), formerly known as Microsoft Malware Protection Center (MMPC), is committed to helping Microsoft customers. With Windows Defender Security Intelligence (WDSI) you can explore in-depth threat encyclopedia for information…
Read more
Foremost is a console program to recover files based on their headers, footers, and internal data structures. This process is commonly referred to as data carving. Foremost can work on image files, such…
Read more
Computers have become a ubiquitous part of our daily lives. Understanding computer basics is essential for anyone who uses a computer, whether it is for personal or professional use. By understanding the fundamental…
Read more
Question 142. Which of the following is often one of the most overlooked areas of security? A. Operational B. Technical C. Internet D. Physical Answer 142. Option D. Explanation: Physical security is one…
Read more
Question 95. What is the Ping of Death? A. Sending packets that, when reassembled, are too large for the system to understand B. Sending very large packets that cause a buffer overflow C….
Read more
Question 48. What is the process of hiding text within an image called? A. Steganography B. Encryption C. Spyware D. Keystroke logging Answer 48. Option A. Explanation: Steganography is the process of hiding…
Read more
Question 1. Which of the following statements best describes a white-hat hacker? A. Security professional B. Former black hat C. Former grey hat D. Malicious hacker Answer 1. Option A. Explanation: A white-hat…
Read more
SEO is undeniably one of the most popular concepts online, gaining attention from experts, developers, website owners, brand, and companies. As website owners strive to be noticed online by the right kind of…
Read more
In a previous tutorial, we used Metasploit Framework to gain a low-level shell on the target system by exploiting the ShellShock vulnerability. The same can also be done by sending a HTTP Request…
Read more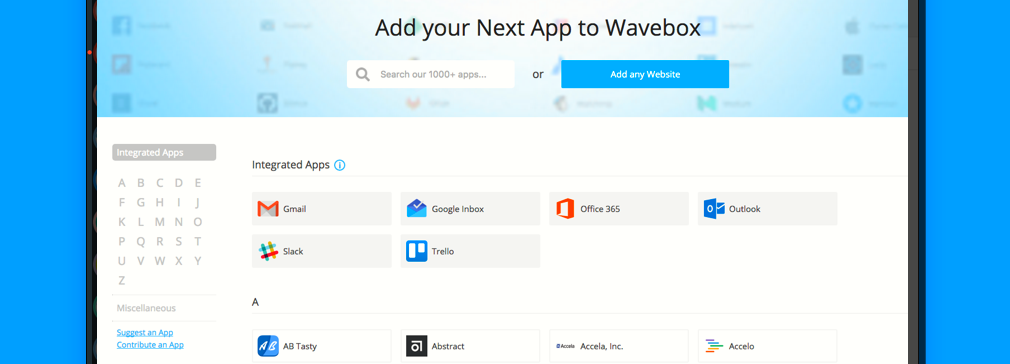
WaveBox is one of the best Email Client for especially Linux distributions but also comes for Windows OS and MacOS which bringing Gmail, Hotmail, Inbox, Outlook etc into a configurable client. Wavebox is built…
Read more
Netstat is truly a very overlooked tool for network troubleshooting so I believe that it would be beneficial to post all of the switches and options available with NETSTAT. Netstat displays protocol statistics…
Read more
Kali Linux is a Linux-based penetration testing arsenal that aids security professionals in performing assessments in a purely native environment dedicated to hacking. Kali Linux is a distribution based on the Debian GNU/Linux…
Read more
WeBaCoo (Web Backdoor Cookie) is a web backdoor script-kit, aiming to provide a stealth terminal-like connection over HTTP between client and web server. It is a post exploitation tool capable to maintain access…
Read more
Headers and methods work together to determine what clients and servers do. This article quickly sketches the purposes of the standard HTTP headers and some headers that are not explicitly defined in the…
Read more