Hack The Box is an online platform allowing you to test your penetration testing skills and exchange ideas and methodologies with other members of similar interests. It contains several challenges that are constantly…
Read more
I hope you all knows the latest vulnerability i.e. Meltdown which has been discovered almost in every CPU having Intel Processor. These both vulnerabilities are basically hardware design flaws that attackers can easily…
Read more
Shodan is one of the world’s first search engine for Internet-Connected devices. With the help of Shodan, you can easily discover which of your devices are connected to internet, where they are located and…
Read more
We assume most of you know what a Man in the Middle (MitM) attack is, but below is a diagram of a Man in the Middle attack. A man-in-the-middle attack is a…
Read more
The best way to put your Wifi adapter to monitor mode is through airmon-ng but with airmon-ng package you can only create a single monitor mode. In this article, you’ll learn how to…
Read more
In this article, we’ll cover two methods through which you can easily test your website loading speed and some other performance factors like Lookup Time, Connect Time, Pre-Transfer Time and Start-Transfer Time. To…
Read more
Kali Linux is the most recent live disk security distribution released by Offensive Security. The latest version i.e. Kali Linux 2017.3 has over 600 security and penetration testing tools included, categorized into helpful groups most…
Read more
As we’ve discussed earlier, that how we actually deauthenticate a wireless device with the help of aircrack-ng tool suite package by flooding a network with deauthenticate packets. To deauthenticate any wireless device/router/client, its…
Read more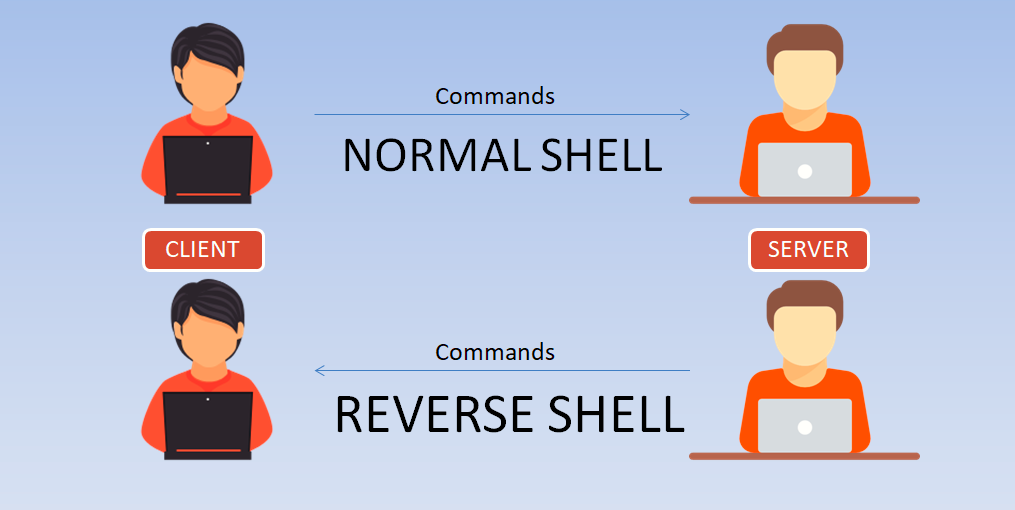
Today we’re are going to show you how to make a reverse shell of any Linux machine. Here in this scenario, we are using two linux based VMs, One is Kali Linux(2017.2) and…
Read more
For decompiling an android application, the open source tool which we’ll use is “dex2jar“. Download Link – Dex2jar.zip (Extract in any location) Sample Application – yeahhub.apk (Download & Extract/Move into dex2jar folder) About…
Read more
SubBrute is one of the most popular sub-domain brute forcing tool through which we can easily enumerate the best possible sub-domains of any domain along with all DNS records. It is one of…
Read more
WPA/WPA2 vastly improves the security of wireless networks; however, the extra protection comes at the price of added complexity to the protocol. Although WPA was developed with security in mind, it does have its own…
Read more
The Apache Web server is a remarkable piece of software. The basic package distributed by the Apache Software Foundation is quite complete and very powerful, and a lot of effort has gone into keeping…
Read more
In general, leaking unnecessary information about software behavior significantly aids an attacker in finding weaknesses within your application. Examples include software version information that can be used to footprint a potentially vulnerable version of…
Read more