In previous article, we got to know that how to install and configure OpenSSH Server in Kali Linux. Now today we’ll see how to crack the password of SSH remotely. Generally SSH uses…
Read more
SSH is an acronym which stands for Secure Shell, which provides a secure shell access to a remote machine. This allow people to connect to a local and remote computer, and it comes…
Read more
SSL Kill is a forced man-in-the-middle transparent proxy that modifies HTTP requests and responses in order to avoid SSL and HSTS, to achieve that, it use a two-way ARP spoofing plus a forced…
Read more
Pythem is a multi-purpose pentest framework written in Python. It has been developed to be used by security researchers and security professionals. The tool intended to be used only for acts within the…
Read more
Before to starting, we’ll setup a virtual pentesting lab with the help of Web For Pentester toolkit which is totally based on Debian OS. As you all knows most of the web applications…
Read more
Well with the help of honeypot, you can easily monitor your own OS and can track every activity of the hacker or you can say that, its the best way to hack the…
Read more
Exploit-DB is one of the most popular platform for their collection of exploits and whitepapers related to Linux/Windows/Assembly/Web/DOS etc. Exploit-DB is the ultimate archive of exploits, shellcode, and security whitepapers. You can easily…
Read more
Q151. Fill in the blank: ____________ tags surround each item in a select menu. Answer – option tags surround each item in a select menu. Q152. True/False: The fieldset tag is used to…
Read more
A web page is composed of multiple features. There are so many SEO tools are also available through which you can also boost your SEO ranking in short manner. Here are the ones…
Read more
Technology advances have significantly changed our lives during the past decade. We rely on computers of various sorts for even the simplest of daily tasks and become stressed when they are not available…
Read more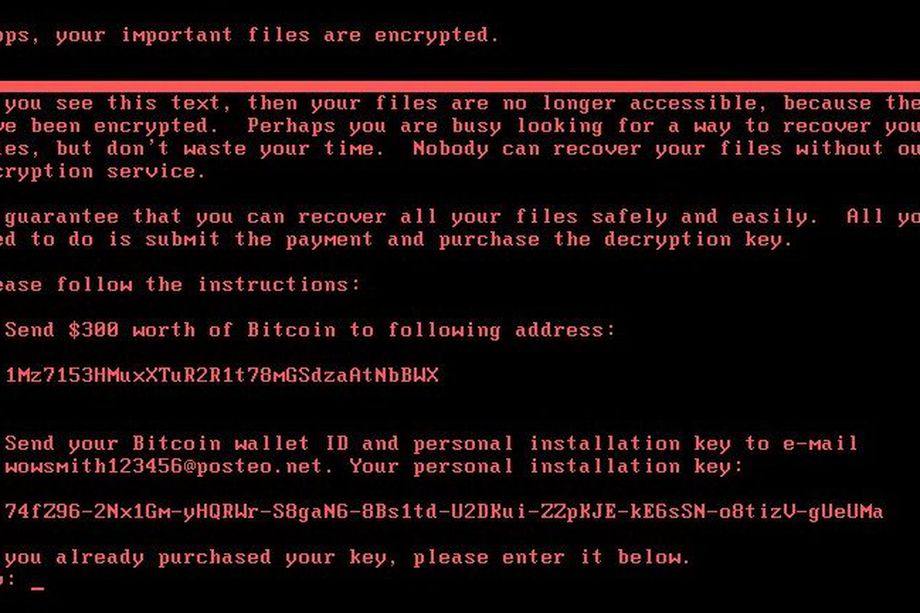
As you all knows, recently Petya Ransomware comes into existence and affected more than 65+ countries. Many organizations in Europe and the US have been affected by this ransomware attack. Although its not…
Read more
As you all knows Wannacry or Wcry Ransomware already created a havoc across the globe and now within the span of just 2 months, a new ransomware named as Petya Ransomware hits globally…
Read more
Today we are introducing a new tool called as “MINIPENGUIN” through which you can easily hack the current user accounts of KALI Linux OS. Mimipenguin is a tool which helps you to dump…
Read more
Q126. True/False: To add a caption to a table, you use the caption attribute in the opening table tag. Answer – False. Q127. If you include a thead or a tfoot group in…
Read more
Whether you want to start a website for fun or to make money, you’ll first have to learn how to make a website. Making a website is not difficult at all. In fact…
Read more