Q201. What two words should be avoided as link labels on a web page? Answer – “Click here” should be avoided as link labels on a web page. Q202. Fill in the blank:…
Read more
Previously we exploited a SQL injection vulnerable website with one of the most popular automated tool called as SQLMAP and now in this article, we’ll try to exploit the similar vulnerable website manually…
Read more
Weak or home-grown algorithms A common mistake developers make is to use weak or flawed encryption/hashing algorithms. For example, many developers use md5 or sha1 as their hashing algorithm of choice. Using a…
Read more
A bug bounty program is a deal offered by many websites and software developers by which individuals can receive recognition and compensation for reporting bugs, especially those pertaining to exploits and vulnerabilities. And…
Read more
WP-Grab-Info is an open source tool through which you can easily detect the WordPress Version, Username, Theme Name and Plugins List. Install WP-Grab-Info in Kali Linux – To install this above said tool,…
Read more
Hello geeks, today we’ll show you some basic SQL Injection techniques with the help of Python and SQLMap. SQL injection is one of the most critical vulnerabilities till now and is still included…
Read more
The Tor Project just announced the launch of a public bug bounty program where you can easily earn the money in between $2,000 and $4,000 for high severity flaws. The Tor’s Bug Bounty…
Read more
Equifax Inc. is a consumer credit reporting agency in the United States, considered one of the three largest American credit agencies along with Experian and TransUnion. Equifax is the oldest of the three…
Read more
Security is a state in which we ensure a proper gap between the threats and assets of an organization. We try to either move assets far away from threats or we try to…
Read more
The LaZagne project (A password recovery tool) is an open source application used to retrieve lots of passwords stored on a local computer. Each software stores its passwords using different techniques (plaintext, APIs, custom…
Read more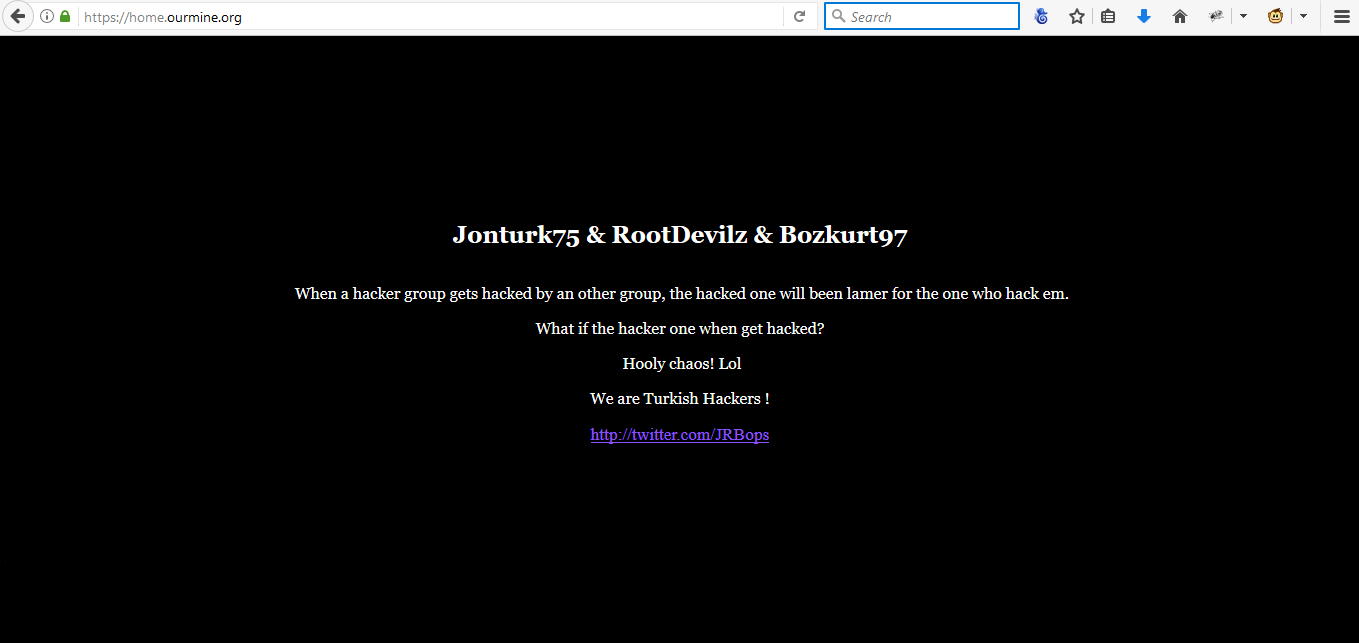
OurMine is a security hacker group based on Saudi Arabia and recently this week, they hacked WikiLeaks.org website with DNS Poisoning Attack. In a statement shared on the Twitter account of one OurMine…
Read more
Windows 10 helps you reduce the cost and complexity historically associated with managing and deploying Windows devices. With Windows as a service, you receive a continuous innovation so you are always up to…
Read more
Good password practices are critical for the following reasons: The most common form of attack on a corporate system is password guessing. On most systems, most untrusted services are protected primarily by passwords…
Read more
Ethereum is the one of the 2nd most popular digital currency after Bitcoin. As per latest stats ref. 1st Sept 2017, the value of 1 BTC and 1 ETH is: 1 BTC =…
Read more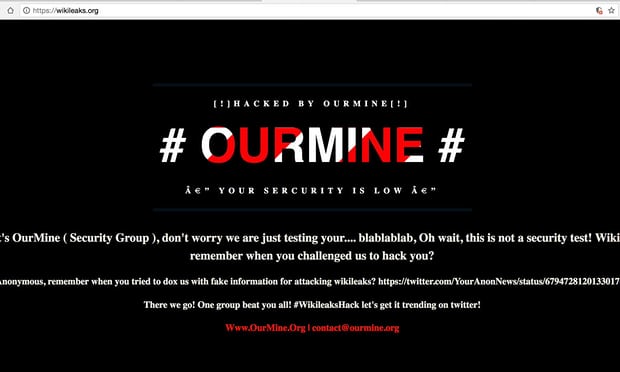
Another defacement attack just happened and this time wikileaks.org website has been hacked by OurMine Hacker which is a Saudi Arabian Hacking group who hacked so many websites last year. The group appears…
Read more
Selena Gomez’s instagram account was suddenly taken down on Monday i.e. on 28th August 2017 by anonymous hacker and posted some nude photos of Justin Bieber (which is the ex-boyfriend of selena) with…
Read more
SQL injection is one of the most prominent vulnerabilities for web-based applications. In last article, we’ve used viSQL through which we scanned the whole server for SQL Injection vulnerabilities with the help of…
Read more
vBulletin is a professional, affordable community forum solution. It gives you an instant community that lets your users to interact, take part in discussions, ask questions, give answers and express opinions. The latest…
Read more